Note: I started with using volatility on my Windows machine, and eventually, I transitioned to working on my Linux machine. Pardon me for screenshots from different OSes.
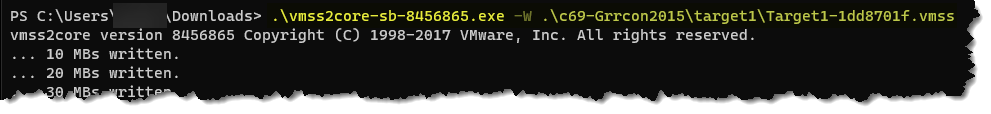
The first task in this challenge is to convert the VMWare Suspended State (.vmss) files to a memory dump so we can perform memory analysis. There is a tool called vmss2core to help us with this first task. To run the conversion, use the command:
vmss2core.exe -W the_vmss_file:
Once the conversion is done, you should see a file, memory.dmp:

The second task is to find out which profile to use within volatility. Volatility needs to know what type of system the memory dump came from so it knows which data structure, algorithm, and other information to use. To find out the profile, run the command:
volatility.exe -f .\memory.dmp imageinfo

Now, we are ready to answer the questions:
Machine: Target1
- What email address tricked the frontdesk employee into installing a security update?
- t***********@*****.com
Use volatility’s yarascan, a plugin that scans the memory image for yara signature. The question asks us to look for the sender of the email. The best way to do it is to search for a matching simple string like “FROM:” Run the command:
volatility.exe -f .\memory.dmp –profile Win7SP1x86_23418 yarascan -Y “From:”

- What is the filename that was delivered in the email?
- a******************.exe
- Since we know that the file was delivered through an email, we have to find the PID of Outlook before we can do a memory dump specifically on Outlook. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 pslist | grep -i outlook

2. Perform a memory dump of the Outlook process using PID 3196. Run the command:
vol.py -f vmss.core –profile Win7SP1x86 memdump –dump-dir . -p 3196

3. We know that we are looking for a file with a .exe extension. Extract the text from the .dmp file using the strings command and pipe the results and grep with .exe. Run the command:
strings -n 10 3196.dmp | grep .exe

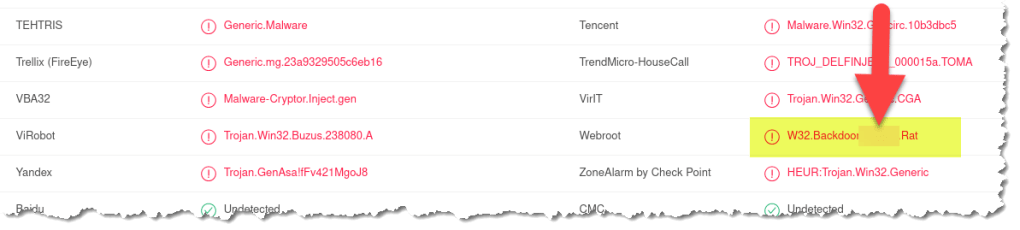
- What is the name of the rat’s family used by the attacker?
- X*****RAT
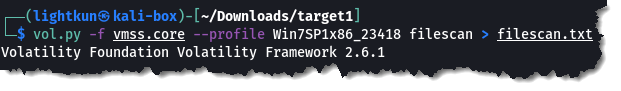
- We need to find the offset of the .exe from the previous question. We can do this by doing a file scan in volatility. This will list all file objects in the image file. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 filescan > filescan.txt
2. Look inside the filescan.txt file to and search for the offset of the .exe in question number 2. Run the command:
cat filescan.txt | grep -i a*********

3. After obtaining the offset of the file that was delivered through email, perform a dumpfile using the offset. When performing a dumpfile, you don’t have to include the leading zeroes of the offset. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 dumpfiles –dump-dir=dumpfiles -Q 0x3df1cf00

4. Locate the result of your running the dumpfiles, and generate a hash off the file. In this example, I am generating an MD5 hash value. Run the command:
md5 file.None.0x85d12b18.dat

5. Open your choice of browser and visit Virustotal. Search using the MD5 value you got from the previous step.

6. Locate the RAT family used by the attacker:
- The malware appears to be leveraging process injection. What is the PID of the process that is injected?
- 2***
- You can use the same Virustotal results from the previous question.
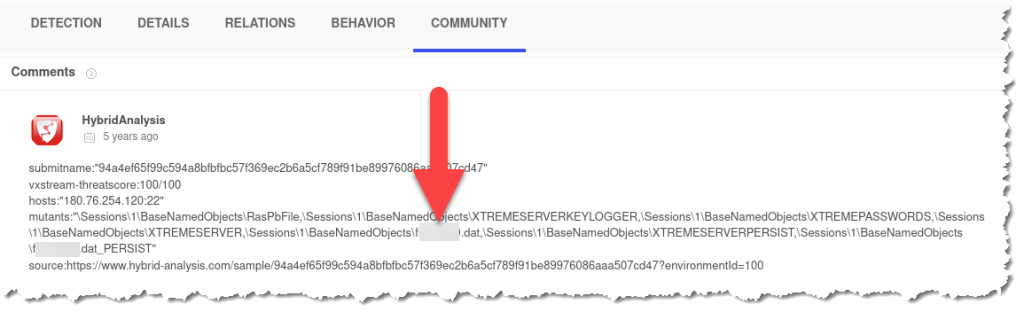
- What is the unique value the malware is using to maintain persistence after reboot?
- M******
- Use the same Virustotal results.
- There are many locations in a Windows OS where an attacker can setup persistence to maintain access to the victim machine even after a reboot. One of the many locations that fall under autostart extension is found in the registry key:
HKCU\Software\Microsoft\Windows\CurrentVersion\Run
3. Thus, when we look at the Virustotal result and go to the Behaviors tab, you will see an entry for “Registry Key Sets.” Here you will see the unique value that is used for persistence:

- Malware often uses a unique value or name to ensure that only one copy runs on the system. What is the unique name the malware is using?
- f********.dat
- It appears that a notorious hacker compromised this box before our current attackers. Name the movie he or she is from.
- h******
This was a lucky guess for me. There are not many movies about hacking, so I could guess it pretty easy.
- What is the NTLM password hash for the administrator account?
- 7940****************************
You will have to do a hashdump to retrieve the password hash. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 hashdump

- The attackers appear to have moved over some tools to the compromised front desk host. How many tools did the attacker move?
- *
- What is the password for the front desk local administrator account?
- f********@****
We will be using the consoles plugin to answer this question. The consoles plugin extracts command history by scanning for command history. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 consoles

We can see here that the attackers ran the command wce.exe -w, which resulted to the showing/extraction the users’ passwords:

- What is the std create data timestamp for the nbtscan.exe tool?
- 2015-**-** 10:**:** UTC
The consoles plugin above will show us the partial answer to this question:

To get the the entire timestamp, we will utilize the timeliner plugin in volatility. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 timeliner | grep -i nbtscan.exe

- The attackers appear to have stored the output form the nbtscan.exe tool in a text file on a disk called nbs.txt. What is the IP address of the first machine in that file?
- 1*.*.*.*
- You need to find the offset value for the file nbs.txt. Let us use the text file that we have as a result of running the filescan plugin earlier. To find the offset value, do a grep of the file nbs.txt in the filescan.txt. Run the command:
cat filescan.txt | grep -i nbs.txt

2. Now that we got the offset value of nbs.txt, we need to use the plugin dumpfiles. The dumpfiles is used to extract memory-mapped and cached files. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 dumpfiles -Q 0x000000003fdb7808 -D ./

3. Look for the extracted file and open it using the cat command. Run the command:
cat file.None.0x83eda598.dat

- What is the full IP address, and the port was the attacker’s malware using?
- 1**.**.***.***:**
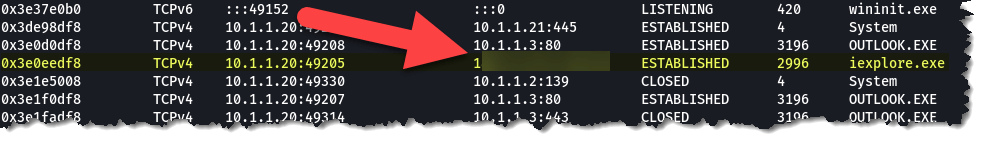
To check for network information, we will use the netscan plugin. Remember that the malware used the process iexplore.exe earlier in our investigation. Once you get the result from running the netscan, look for the IP address associated with the iexplore.exe process. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 netscan

- It appears the attacker also installed legit remote administration software. What is the name of the running process?
- t*********.exe
The answer to this question can be obtained by using the pslist plugin. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 pslist

- It appears the attackers also used a built-in remote access method. What IP address did they connect to?
- 1*.*.*.**
We know that the machine we are investigating is running a Windows OS and that the built-in remote access method is mstsc. Use the netscan plugin again and look for mstsc.exe process. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 netscan | grep -i mstsc.exe

Machine: Target2
Same as with the very first task we had to do before we could answer questions for the Target1 machine. We have to convert the .vmss file to a dump file and find out which profile to use so we can use volatility to analyze the file.
It looks like we are using the same profile on target2: Win7SP1x86_23418
- The attacker moved laterally from the front desk machine to the security admins (Gideon) machine and dumped the passwords. What is Gideon’s password?
- t*******
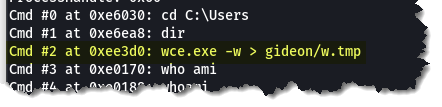
- Let’s check what commands were executed by the attackers by using the consoles plugin. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 consoles
2. We also know from the target1 machine that the attackers used the command wce.exe to get the users’ passwords. From the result of running the consoles plugin, we can see that the wce.exe was used again, and the results were written in gideon/w.tmp:
3. Next is to do a filescan. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 filescan > filescan.txt
4. From the filescan result, we will find out the offset value of the w.tmp file. Run the command:
cat filescan.txt | grep -i w.tmp
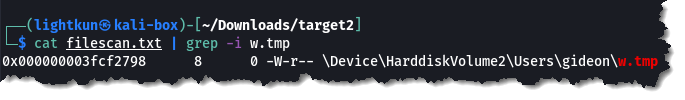
5. Now that we have obtained the offset value, let’s do a dumpfile. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 dumpfiles -Q 0x3fcf2798 -D ./

6. Finally, just open the dump file with the cat command. Run the command:
cat file.None.0x85a35da0.dat

- Once the attackers gained access to “Gideon,” they pivoted to the AllSafeCyberSec domain controller to steal files. It appears they were successful. What password did they use?
- 1*****!@#
The use of consoles plugin is the way to do it. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 consoles

- What was the name of the RAR file created by the attackers?
- c**********.rar
You can use the screenshot just above this question to get the answer.
- How many files did the attacker add to the RAR archive?
- *
This was tricky because the question was asking for the number of files, and in reality it is asking for all .txt files, and not all files. I should have been more observant because, going back to the use of the consoles plugin, it was obvious that all files added to the rar archive were all .txt extension files.
- The attacker appears to have created a scheduled task on Gideon’s machine. What is the name of the file associated with the scheduled task?
- 1.***
- First, we have to list what is possible scheduled tasks are in our filescan.txt file: Run the command:
cat filescan.txt | grep -i “System32\\\tasks\\\\”
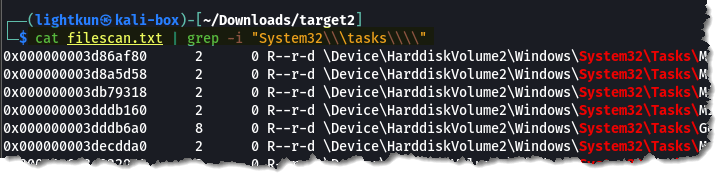
We can see in the next image that there is one file naming convention that stands out:
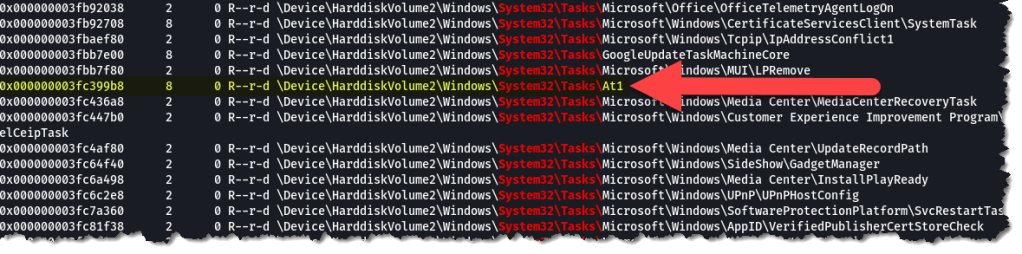
2. Now that we have obtained the offset value, we can use dumpfiles to extract its content. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 dumpfiles -Q 0x3fc399b8 -D ./

3. Check the content of the extracted file and look for the associated file:

- What is the malware CNC’s server?
- 5*.**.***.**
Run the netscan plugin to get the answer. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 netscan

- What is the common name of the malware used to infect the POS system?
- d*****
- Running the malfind plugin, there are two iexplorer.exe processes that can be associated to the malware.
- Extract a dump file by running the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 malfind -p 3208 -D ./
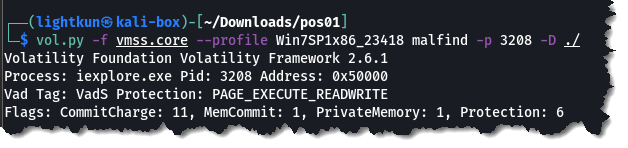
3. Now, that we got the dump file, upload it to Virustotal:

- In the POS malware whitelist. What application as specific to Allsfecybersec?
- a******_*********.exe
- Dump the dll of the 3208 pid. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 dlldump -p 3208 –base=0x50000 -D ./

2. And since we are looking for a .exe file, we will use strings and grep exe. Run the command:
strings module.3208.3fd324d8.50000.dll | grep -i exe

- What is the name of the file the malware was initially launched from?
- a******_******.exe
By using the iehistory plugin, we can locate the filename. Run the command:
vol.py -f vmss.core –profile Win7SP1x86_23418 iehistory


This was one of the longest blogs entry/write-ups I’ve done. I hope you will find this helpful. I really enjoyed working and completing this challenge. Shout out to CyberDefenders.org.
Please subscribe to my blog if you haven’t done so.

Yeah, pardon YOU is right. Windows….SMH. 😉 Great write-up as usual!
LikeLike