The good stuff first
I woke up at 4:30 AM to take a leak, and just had a feeling to check my email quick before jumping back to bed. And then I saw the best email I could ever wish for from Security Blue Team:

Needless to say, I was not able to go back to sleep that morning. The excitement and elation kept me awake. All the late nights and time I sacrificed- not playing with my kids or snuggling with my wife- eventually paid off.
Want to know what some of that time looked like for me? Here’s a sped up version of my first 12 hours taking the practical exam. Cue my ever-increasing amount of mental anguish over time, while questioning more and more whether I bit off more than I could chew attempting this certification:
Now that we’ve had a good laugh at my expense, let’s cover the basics:
Who is Security Blue Team (SBT)?
Security Blue Team is a company producing high quality community events, including CTFs, defensive security operations and training labs. SBT also offers practical defensive cyber certifications, backed by an Academic Advisory Board comprised of 8 industry experts.
SBT’s LinkedIn Page
What is the Blue Team Level 1 certification?
A hands-on defensive training course and certification, showcasing practical ability in defending networks and systems from cyber threats. No more multiple-choice exams – get genuine security operations experience with a realistic incident response scenario in our 24-hour practical assessment.
– SBT’s website: http://securityblue.team
Who is the BTL1 course for?
BTL1 is perfect for security enthusiasts or professionals that want to develop their practical defensive cyber skills.
– SBT’s website: http://securityblue.team
What is included in the BTL1 course?
The course covers six domains in detail:
- Security Fundamentals
- Phishing Analysis
- Threat Intelligence
- Digital Forensics
- SIEM
- Incident Response
The course also includes 2 free certification attempts. If you fail your first attempt, you will have another free shot at the practical test but only after 10 days from your initial attempt. The opportunity to re-sit the exam if you fail is a great indication that the company would like to see the candidate succeed, and that they know that they have created the exam to be a real challenge that there is a real chance that not everyone will pass the test on their first try.
How was the course?
The course felt like a product that was put together with so much thought and care from the minds of those who wish they had these kind of course and training when they started their careers in cyber security. The following are the things that impressed me the most in the course:
- The presentation was not in Powerpoint slides. For some reason, something is in Powerpoint slides that is equivalent to the word boring. See image below on how clean and simple the presentation is:
Even the course navigation column looks neat and it is not easy to get lost from where you left off when taking a break:

2. The quizzes are relevant, come in different formats, and not just multiple choice questions. These formats include (see also the example below each format category):
a. Fill in the blank (You will have to perform some hands-on activity to answer the questions):

b. Multiple choice:

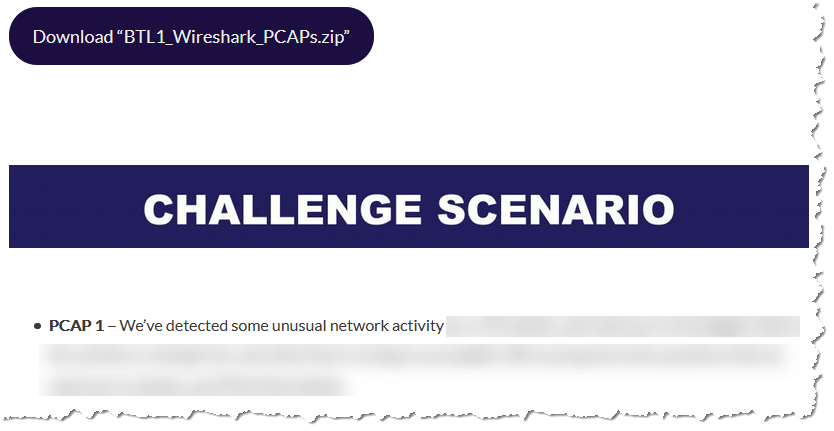
c. PCAP analysis:
d. YARA writing:

Also, you will see a lot more formats such as SIEM usage and analysis, Phishing analysis and Forensics investigation.
3. There are not a lot of videos included but when there is one, it is professionally done, short and direct to the point. Just look at the image below, that is the desktop background used in the videos. It presents as both clean and well-made.

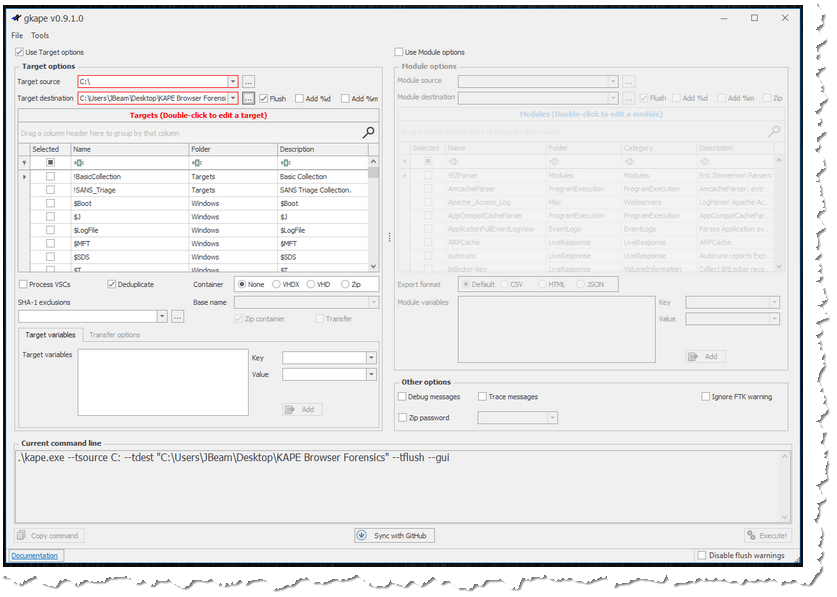
4. Instructions with screenshots are included on how to use the tools that they want you to learn how to use, like the use of KAPE below:
5. To start the certification exam, there is no need to wait for a proctor- which in my experience, has sometimes been the cause of the delay when taking a proctored exam. All you need to do is agree to the NDA, click the “Launch Exam Lab” and your lab environment is ready in under 2 minutes.

How was the practical certification exam?
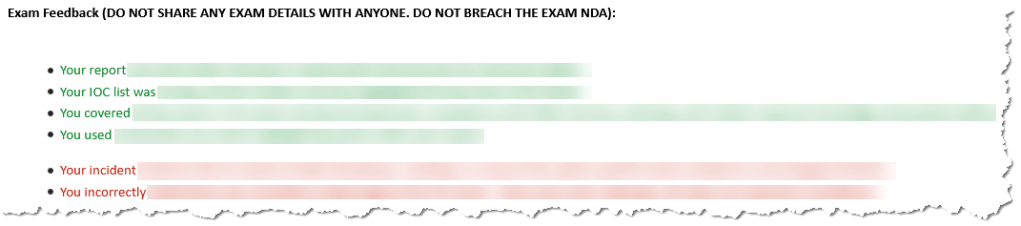
The certification exam is a 24-hour practical test. The first 12 hours is dedicated to going through the lab environment to gather as much information, evidence and IOCs you can. Then, the lab access ends, and the next 12 hours is left to write the incident report, which will be hand-marked by the person reviewing your report. Below is the personalized feedback I received from my report. After reading the feedback and looking back at my report, the feedback are spot-on:
The lab is a browser-based environment. There is no need to download a VPN configuration file, and you will not have to worry about nagging thoughts in your head of the VPN will/might get disconnected. I never had a single issue with the lab. In fact, my lab experience was seamless. You will be provided with a scenario, and off you go on your own- all while hoping you prepared enough and took notes when you went through the course.
Most notably, I sincerely appreciated the exam being created to feel like a real-life scenario of a company getting breached by malicious actors. It reminded myself (and I feel safe to assume other examinees) of the weight of importance this certification carries and why those like myself have sought this training in the first place.
What is your advice for those who plan to take the BTL1?
The best advice I can give is to NOT UNDERESTIMATE the exam. If you were able to complete all the quizzes and activities during the course- pat yourself on the back, and then be prepared to be humbled. Completing such means you have the basic knowledge to tackle the exam, but is that alone is not enough to pass it? I would say- well, it depends.
If you don’t have any experience analyzing logs or the use of SIEM then you will need more practice. Remember that this certification exam is geared towards blue team and analyst roles- meaning you will not be breaking into systems, but you will have to spend a lot of time analyzing data to track down and follow the crumbs left by the attackers. You will have to study and ask yourself: “‘How the attackers gained initial access to your environment?’, ‘What execution techniques were used?’, ‘How did the attackers maintain persistence?’, ‘Did they use vertical or horizontal privilege escalation?’, ‘Were there any defensive evasions taken?’, ‘How about any data exfiltrated from your environment?’, ‘Were there any accounts compromised?’, ‘How was the breach discovered?’, and ‘What impact does the breach have to the company?'” These are all part of the ATT&CK MATRIX framework.
My biggest takeaways from the course:
- My digital forensics knowledge and skills were improved. The ability to gather Windows and Linux evidence, analyzing memory dumps, the use of Autopsy to investigate and FTK Imager to create digital forensics copy have also improved.
- I am more comfortable to use YARA in Incident Response’s detection and analysis.
- My ability to analyze, investigate and take defensive actions against phishing emails has increased.
- I now have a greater appreciation of the ATT&CK MATRIX framework to identify and recognize the TTPs that the attackers used, and to better provide defense against attackers.
- I have gained better understanding of the importance of Threat Intelligence.
- My weakest skill of report writing was definitely put to test on this exam.
- If I were a hiring manager, either I will make this certification a requirement to get into a SOC Analyst role, or make it a requirement to pass the certification some time after they get hired. Those who have taken the BTL1 will understand why I mentioned this- the exam is no joke.
Conclusion:
I consider this certification as the gold standard for any SOC Analyst because by passing the practical exam, one has demonstrated they obtain the ability to defend networks and systems from cyber threats; have basic knowledge across 5 security operations domains that Security Analysts normally work with, which include: phishing analysis, digital forensics, threat intelligence, SIEM and incident response; and exhibit they can write incident reports clearly enough for both technical and non-technical audience to read and understand.
I hope you enjoyed my blog post. Please don’t forget to subscribe so you will get notified when I upload new contents.
*****UPDATE*****
5/24/2021 – Received the hard copy certificate, gold coin, and stickers on the mail today. Check out my opening of the certificate:

The first line….ha! But seriously, SO awesome and congratulations.
LikeLiked by 1 person
Thanks for sharing, very interested in BTL1 as well, love the practical aspect of it!
LikeLike
AAAwesome! Congrats the gold coin Babe! would you be able to write about your study process time involved, any outside resources used, books. videos. Im looking forward to a Gold coin as well .
LikeLike