This room was released on 11/25/2021 and it is rated medium in difficulty. Shout-out to the room creators, RussianPanda [She/Her] and Heavenraiza. You can access the room at https://tryhackme.com/room/c2carnage.
This is another blueteam side of the cybersecurity field. The skills/tools to be tested and needed to complete this challenge are WireShark, VirusTotal, and Malware and Network Traffic Analysis.
I intentionally masked parts of the answers so you will have to perform some hands-on work to find the entirety of the answers. This was great room to practice network traffic analysis using Wireshark.
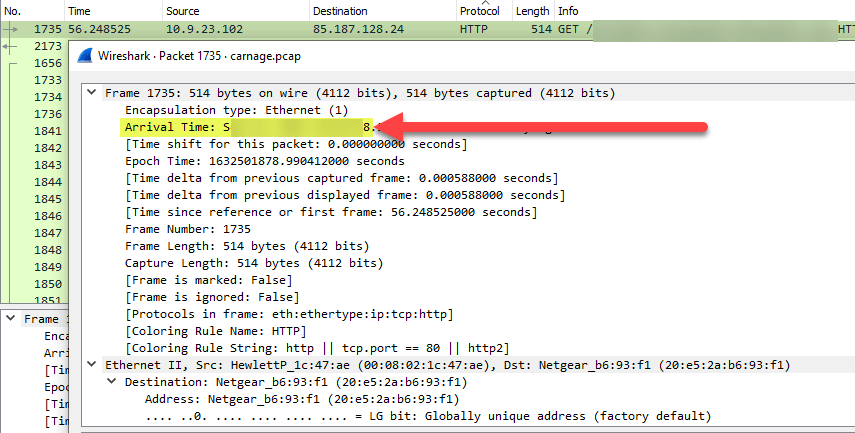
- What was the date and time of the first HTTP conenction to the malicious IP?
- 2***-**-** **:**:*8
- Filter the packets to only show HTTP.
- Type http in the filter tab and hit Enter.
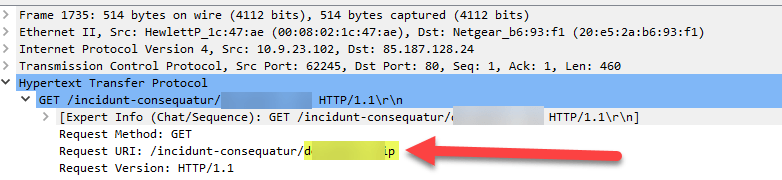
- What is the name of the zipped file that was downloaded?
- d********.**p
Looking at the same packet 1735 as the image from the previous question.
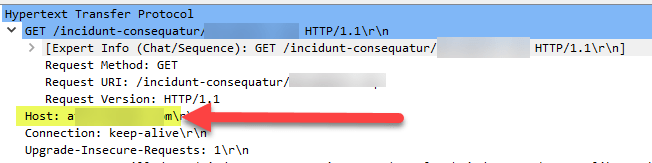
- What was the domain hosting the malicious zipped file?
- a**********.**m
Again, from the same packet, 1735. We can find the hostname.
- Without downloading the file, what is the name of the file in the zipped file?
- c****-**********.**s
- Filter the packets to only show HTTP.
- Right-click on any HTTP packet.
- The hover your mouse to Follow > TCP Stream.
- Look within the stream and you will find the name of the file without downloading the zipped file.
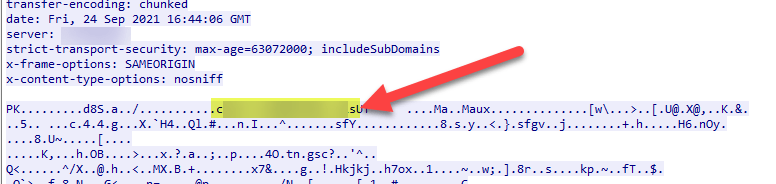
- What is the name of the webserver of the malicious IP from the which the zipped file was downloaded?
- L*******d
From the same TCP stream 73 as the previous question, you will find the name of the webserver.
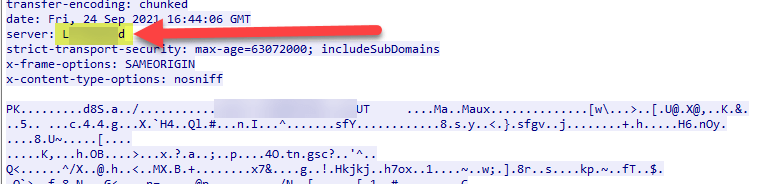
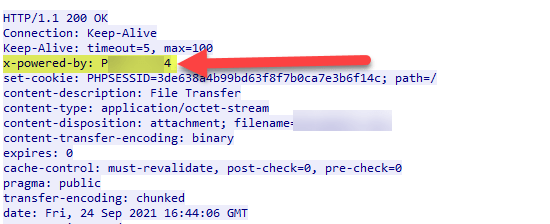
- What is the version of the webserver from the previous question?
- P**/*.*.*4
The same information can be found in TCP stream 73.
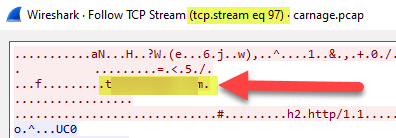
- Malicious files were downloaded to the victim host from multiple domains. What were the three domains involved with this activity?
- f*********.***.*u, t*********.**m, n**.*********.**m
- The creators of the room provide a hint to filter HTTPS traffic and the timeframe of 16:45:121 to 16:45:30.
- To use the hints from the creators fo the room, I used the filter tcp.port == 443 and (frame.time >= “Sep 24, 2021 10:45:11”) && (frame.time <= “Sep 24, 2021 10:45:30”).
- The tcp.port 443 is for the HTTPS traffic, and the times I used was different because I download the PCAP file locally to my machine and the timestamp automatically converted to US Mountain Standard Time, and I think the original time used in this challenge is in UTC, so I had to convert the room creators’ hint to Mountain Standard Time.
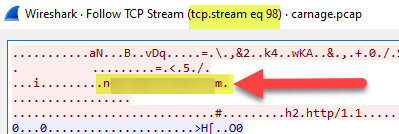
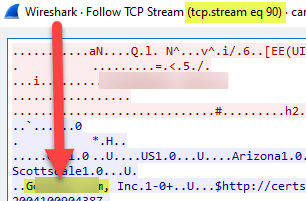
- Once you have applied the filter from Step 2, you just have to do the same steps to follow the TCP streams. The three streams that contain the multiple domains are 90, 97, and 98.
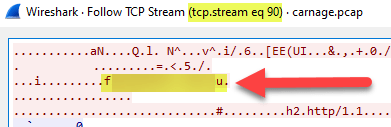
- Which certificate authority issued the SSL certificate to the first domain from the previous question?
- G*****y
Since it is asking for the first of the three domains from the previous question, we will have to look at the TCP Stream 90.
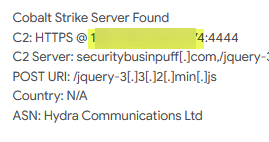
- What are the two IP addresses of the Cobalt Strike servers? Use VirusTotal to confirm if IPs are identified as Cobalt Strike C2 servers.
- 1**.***.**.**8, 1**.***.***.**4
When filtering the packets to only show HTTP packets, there are external IP addresses that the victim IP was communicating with. The creators of the room’s instruction are to find the IPs that are identified as Cobalt Strike C2 through VirusTotal. I entered the external IP addresses on VirusTotal and found the answers.
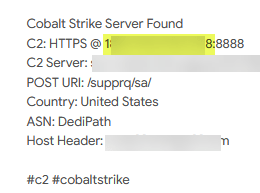
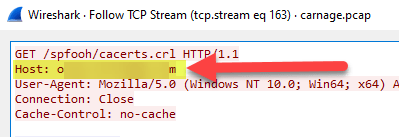
- What is the Host header for the first Cobalt Strike IP address from the previous question?
- o***.********.**m
- Filter to only show packets that include the first IP address from the previous question.
- The filter I used was ip.addr == 1**.***.**.**8.
- Then continue to follow the stream.
- The stream to use is 163.
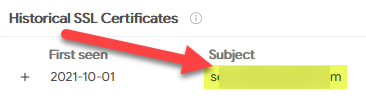
- What is the domain name of the first IP address of the Cobalt Strike server?
- s********.***e
This can be found by entering the first C2 server IP address to VirusTotal.

- What is the domain name of the second Cobalt Strike server IP?
- s****************.**m
Same process as the previous question. Use VirusTotal.
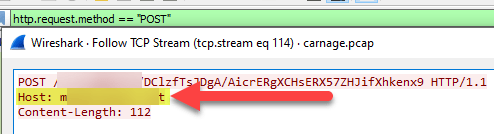
- What is the domain name of the post-infection traffic?
- m**********.**t
- Filter to show just the HTTP packets.
- And also include to filter POST requests.
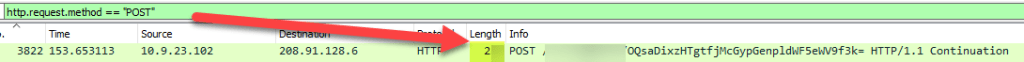
- The filter I used was http.request.method == “POST”.
- Now, investigate TCP stream 114.
- What are the first eleven characters that the victim host sends out to the malicious domain involved in the port-infection traffic?
- z*********9
Using the same filter from the previous question, you will see the first 11 characters being sent out.
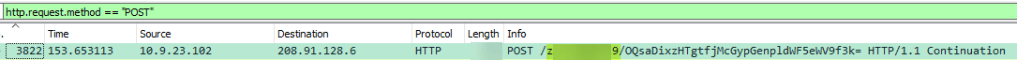
- What was the length for the first packet send out to the C2 server?
- 2**
Using the same image from the previous question, you will see the length information too.
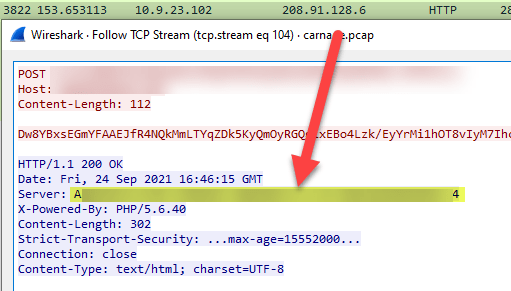
- What was the server header for the malicious domain from the previous question?
- A*****/*.*.** (******) *******/*.*.** ***_*********/*.4
- Right click on the packet from the previous question.
- It will open up TCP stream 104.
- And you will see the server header under Server.
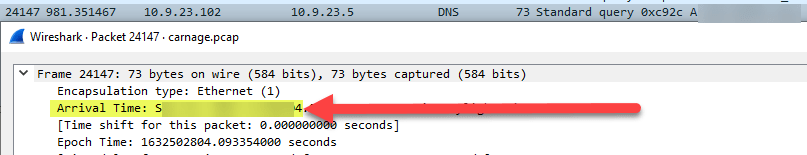
- The malware used an API to check for the IP address of the victim’s machine. What was the date and time when the DNS query for the IP check domain occurred?
- 2***-**-** **:**:*4
- Filter the packets to only show DNS.
- Check packet 24147.
- You will find the date and time under Arrival Time.
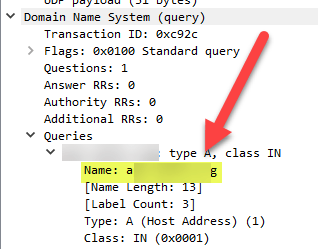
- What was the domain in the DNS query form the previous question?
- a**.*****.**g
Using the same packet from the previous question, you will find the domain.
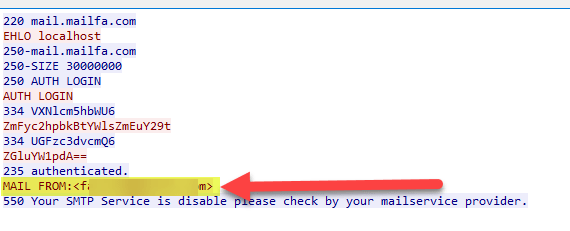
- Looks like there was some malicious spam (malspam) activity going on. What was the first MAIL FROM address observed in the traffic?
- f******@******.**m
- Filter the packets to only show SMTP.
- Right click on packet 28343.
- Choose Follow > TCP Stream.
- TCP stream 383 will open and you will see the Mail From information.
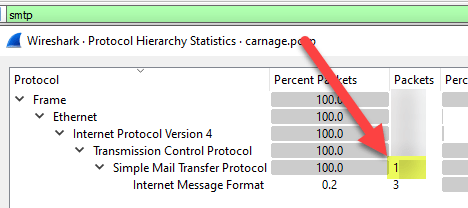
- How many packets were observed for the SMTP traffic?
- 1***
- Filter again to only show SMTP.
- The on WireShark menu, click on Statistics.
- Then click on Protocol Hierarchy.
- And a window pops up that will show you the packet number for SMTP traffic.
I hope you enjoyed my walkthrough of the room. Please don’t forget to subscribe to my blog so you will get notified once I post new entries here.
Hurrah defenders! Hacking is fun! Keep hacking, keep grinding!

Always cool to see Wireshark in action. Great write-up!
LikeLike