This room was released on 8/26/2022 and is rated medium in difficulty. Shout-out to the room creator, @F11snipe. You can access the room at https://tryhackme.com/room/b3dr0ck.

Scenario: Barney is setting up the ABC web server and using TLS certs to secure connections, but he’s having trouble. Here’s what we know:
- He established Nginx on port 80, redirecting to a custom TLS webserver on port 4040.
- There is a TCP socket listening with a simple service to help retrieve TLS credentials (client key & certificate).
- There is another TCP (TLS) helper service listening for authorized connections using files obtained from the above service.
- Can you find all the Easter eggs?
| Party | IP Address |
| My Attack Machine | 10.13.3.31 |
| Victim Host | 10.10.74.107 |
Questions:
- What is the barney.txt flag?
- THM{f******************************c}
- First, let’s do a nmap scan of the victim machine.
- Type nmap -sC -sV -p- 10.10.74.107
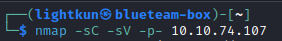
- There are five open ports found: 22, 80, 4040, 9009, and 54321

- Visiting the webserver through port 80, redirects us to port 4040:

- I always look at the list of rooms because it gives you hints on what is included or tools that are expected of you to use to complete the room. For this room, the hints are ctf, tls, socat, sockets:

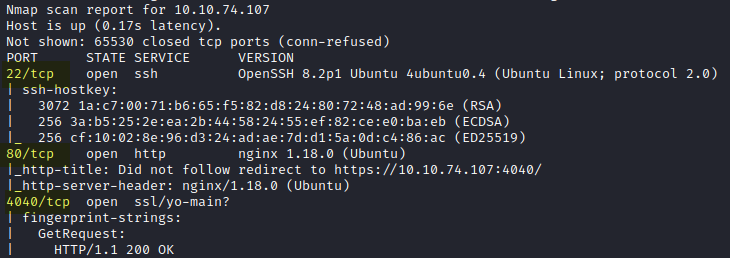
- With the hints, I started looking at how I could use socat. This page helped me access the files necessary to get the initial foothold. I tried the different ports and finally got a positive result with port 9009.
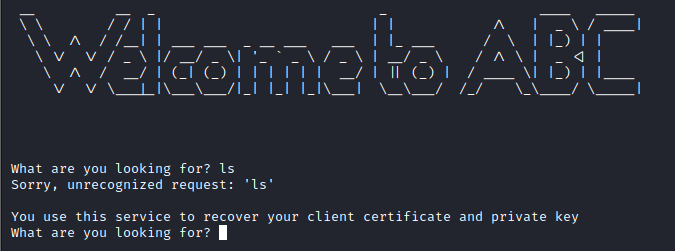
- Type socat TCP:10.10.74.107:9009 – and you will get a response from the server:
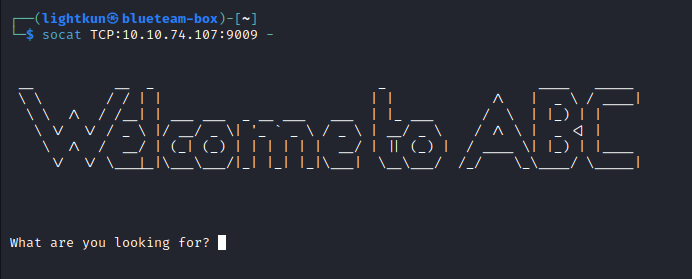
- I always start with the ls command when I see a prompt waiting for interaction. After entering ls, a response was displayed on the terminal, which is also a hint:
- Typing any of the words in the hint will result in the files we need to move on to the next steps. Type certificate:

- Type key:

- I saved both files as certificate for the certificate and key for the key.
- I thought the latter was an SSH private key that I could use to SSH to the victim machine since one of the open ports from our nmap scan is SSH. I was prompted for a password when attempting to SSH using the private key, so I thought I had to extract and crack the password using ssh2john, but that was a dead end. I went back to the socat session I had on port 9009 to see if there were any clues that I missed. Typing –help or just help resulted in the missing clue I have been looking for.

- Type socat stdio SSL:10.10.74.107:54321,cert=<certificate_you_copied>,key=<key_you_copied>,verify=0

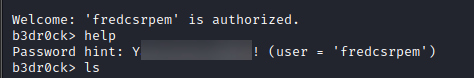
- Now, we get another terminal prompt, so I typed the password because it doesn’t look like a regular terminal prompt again like when we had our initial socat session in the beginning:

- I masked the result above because, at first, I thought it was an encoded string that I had to decode to get the password. I was tricked by the words “Password Hint.” After numerous attempts to decode it, I realized that it wasn’t a hint at all but actually the password itself.
- I SSH to the victim machine using the password above. Type ssh barney@10.10.74.107
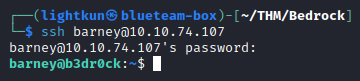
- After successfully logging in via SSH, listing the barney’s home directory will show us barney.txt, which contains the barney.txt flag:


- THM{f******************************c}
- What is Fred’s password?
- Y**************!
- The first I always do when looking for privesc is to list what sudo privileges the current user has. Type sudo -l

- Listing the /home directory, we see another user named fred. But we don’t have permission to access/read the file fred.txt.

- The information we gathered above tells us that we will have to utilize certutil to privesc as fred, since we do have sudo privilege in certutil. Typing certutil -h will show us how to list current certs.

- Type certutil ls

- The above screenshot shows files with fred as the filename. That tells me we can use these files like we did with the user barney. We cannot use cat or any text editors to open any of the files, so we have to do more reading on how to utilize certutil to read the contents of any of the files.
- Type sudo certutil -a fred.csr.pem to retrieve the private key and certificate:

- Then use the socat hint we got earlier when we found user barney’s password. This time we will use the certificate and key for user fred. Type socat stdio ssl:10.10.74.107:54321,cert=<cert_for_user_fred,key=<key_for_user_fred>,verify=0

- Type help or password to retrieve user fred’s password:
- The first I always do when looking for privesc is to list what sudo privileges the current user has. Type sudo -l
- Y**************!
- What is the fred.txt flag?
- THM{0******************************d}
- Now that we have user fred’s password. We don’t need to SSH since we are already on the same box as user barney. All we have to do is switch user by typing su – fred then enter the password we retrieved above:

- To retrieve the flag, type cat fred.txt

- Now that we have user fred’s password. We don’t need to SSH since we are already on the same box as user barney. All we have to do is switch user by typing su – fred then enter the password we retrieved above:
- THM{0******************************d}
- What is the root.txt flag?
- THM{d******************************7}
- We are now logged in as user fred. Let’s check what sudo privilege we have; type sudo -l

- No password is required to use base64. Type sudo /usr/bin/base64 /root/pass.txt
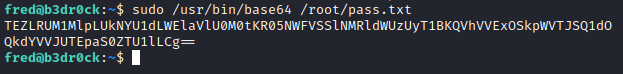
- It looks like a base64 encoded string to me. Let’s use Cyberchef to decode this string. After decoding the base64, we can see that it looks like the string is encoded multiple times. We got another encoded result:

- All we have to do is paste the results above into the input section. And whenever you see a magic wand-looking icon on the output section, use it.

- Hitting the magic wand results in what looks like an MD5 hash.

- Let us use an online resource to crack this MD5 hash, using crackstation.net. This gives us the user root password:
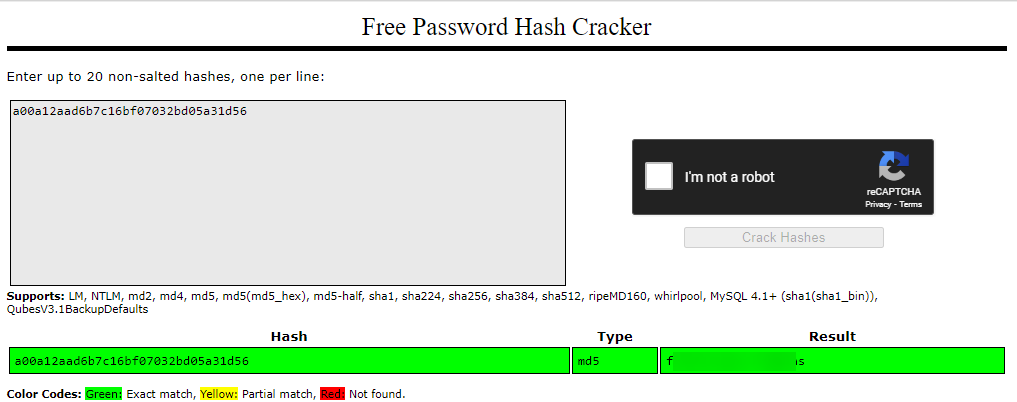
- Now that we have the user root’s password, we can go ahead and type su and use the root password to login as user root:

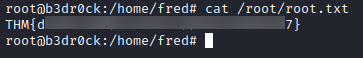
- As user root, we can now get into the root folder and retrieve the contents of root.txt:
- We are now logged in as user fred. Let’s check what sudo privilege we have; type sudo -l
- THM{d******************************7}
Hope you guys enjoyed the walkthrough, and thank you again to @F11snipe for creating this room. I enjoyed it and learned more about certutil as I had to do some reading to understand how to use and exploit using the tool.
Please subscribe to my blog if you haven’t done so.

Rated “medium” but easy for you? I bet so.
LikeLiked by 1 person
Haha, no way man. medium is medium. I struggled and had to do lots of research.
LikeLike